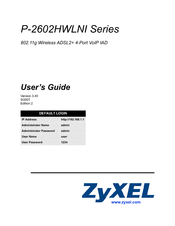
ZyXEL Communications P-2602HWLNI-D3A Manuals
Manuals and User Guides for ZyXEL Communications P-2602HWLNI-D3A. We have 1 ZyXEL Communications P-2602HWLNI-D3A manual available for free PDF download: User Manual
ZyXEL Communications P-2602HWLNI-D3A User Manual (496 pages)
P-2602HWLNI Series 802.11g Wireless ADSL2+ 4-Port VoIP IAD
Brand: ZyXEL Communications
|
Category: Network Router
|
Size: 15 MB
Table of Contents
-
-
Overview41
-
-
Leds46
-
Table 2 Leds46
-
-
-
Login Types50
-
-
Introduction63
-
-
-
Voip Wizard77
-
-
-
Introduction77
-
-
-
Introduction83
-
-
-
Any IP Table91
-
WLAN Status92
-
LED Status96
-
Network99
-
-
WAN Setup101
-
-
-
WAN Overview101
-
Encapsulation101
-
Multiplexing102
-
VPI and VCI102
-
Nat103
-
-
Metric103
-
Traffic Shaping104
-
Traffic Redirect114
-
WAN Backup Setup114
-
LAN Setup117
-
-
-
LAN Overview117
-
Lan Tcp/Ip118
-
RIP Setup120
-
Multicast120
-
Any IP121
-
How any IP Works121
-
DHCP Setup124
-
LAN Client List125
-
LAN IP Alias126
-
Wireless LAN129
-
-
-
-
No Security134
-
Wpa(2)-Psk136
-
OTIST Screen140
-
MAC Filter143
-
Association List145
-
Qos Screen145
-
WDS Screen148
-
Static WEP149
-
Wpa-Psk150
-
Wpa2-Psk152
-
-
-
Port Forwarding159
-
Address Mapping163
-
Voip167
-
Part IV: Voip167
-
Voice169
-
-
Chapter 11 Voice
169-
Sip169
-
SIP Identities169
-
SIP Servers170
-
SIP Proxy Server170
-
Rtp173
-
Voice Coding175
-
-
SIP Qos Screen182
-
Phone183
-
Analog Phone184
-
ISDN Phone189
-
Ext. Table191
-
-
The Flash Key195
-
Speed Dial198
-
PSTN Line206
-
PSTN Line Screen206
-
ISDN Line Screen207
-
Voip Trunking211
-
-
Call Rules213
-
-
Call Progression224
-
Phone Usage227
-
-
Internal Calls227
-
Phone Book228
-
Call Transfer228
-
Call Forwarding228
-
Follow Me228
-
Call Pickup229
-
-
Security231
-
Part V: Security231
-
Firewalls233
-
-
-
-
Packet Filtering243
-
Firewall243
-
-
-
Access Methods245
-
-
LAN to WAN Rules248
-
Alerts248
-
-
-
Dos Thresholds259
-
-
-
-
VPN Overview269
-
Ipsec269
-
VPN Applications270
-
-
Encapsulation271
-
Transport Mode272
-
Tunnel Mode272
-
Ipsec and NAT272
-
VPN Screens275
-
-
-
Ipsec Algorithms275
-
My IP Address276
-
VPN Setup Screen277
-
Keep Alive279
-
Pre-Shared Key283
-
IKE Phases288
-
Manual Key Setup292
-
-
Certificates301
-
-
My Certificates303
-
Trusted cas311
-
Advanced325
-
-
Static Route327
-
-
-
Auto Classifier331
-
-
Http346
-
Telnet347
-
Configuring FTP348
-
Snmp349
-
Configuring DNS352
-
Configuring ICMP353
-
Ssh354
-
How SSH Works355
-
Configuring SSH356
-
-
Upnp and Zyxel362
-
-
System375
-
-
-
Logs387
-
Chapter 27 Logs
387-
Logs Overview387
-
Alerts and Logs387
-
-
Viewing the Logs387
-
Log Descriptions392
-
Troubleshooting401
-
-
Chapter 29 Tools
407-
Introduction407
-
-
Restart413
-
-
Diagnostic419
-
-
-
-
Macintosh os X444
-
-
Java Permissions451
-
-
Network Size455
-
-
-
Preamble Type465
-
-
Antenna Gain473
-
Antenna Overview473
-
-
Index489
-
Advertisement
Advertisement
Related Products
- ZyXEL Communications P-2602HWLNI
- ZyXEL Communications P-2602HW-61C
- ZyXEL Communications P-2602HWNLI
- ZyXEL Communications P-2602HWL-C -
- ZyXEL Communications P2602HW-C -
- ZyXEL Communications P-2602HWLNI-D7A
- ZyXEL Communications P-2602H-D1A
- ZyXEL Communications P-2602H-D3A
- ZyXEL Communications P-2602HL-D3A
- ZyXEL Communications P-2602HL-D7A