LevelOne GTL-2880 User Manual
Hide thumbs
Also See for GTL-2880:
- Quick installation manual (16 pages) ,
- Quick installation manual (16 pages)
Summary of Contents for LevelOne GTL-2880
-
Page 1: User Manual
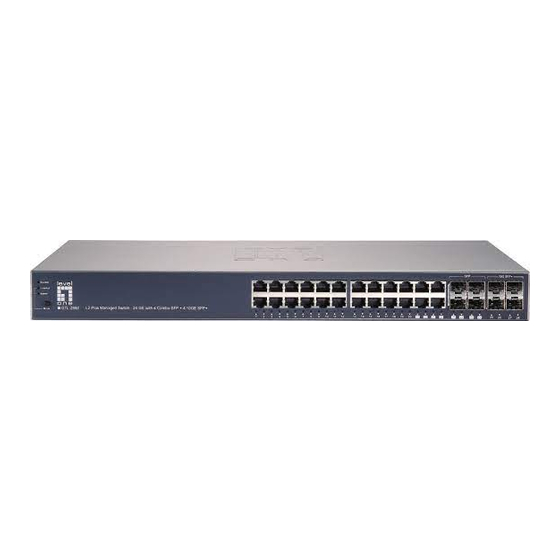
GTL-2880 L2 Plus Managed Switch – 24 GE with 4 Combo SFP + 4 10GE SFP Plus User Manual Ver. V1.1-130827... - Page 2 Product is used in an extra hazardous environment or activities, (4) any serial number on the Product has been removed or defaced, (5) this warranty will be of no effect if the repair is via anyone other than LevelOne or the approved agents, or (6) In the...
- Page 3 LevelOne, then LevelOne will replace the media. LevelOne shall not be responsible for the replacement of media if the failure of the media results from accident, abuse or misapplication of the media.
-
Page 4: Table Of Contents
Table of Contents INTRODUCTION ..............................1 CHAPTER 1 OPERATION OF WEB-BASED MANAGEMENT ............2 CONNECTING NETWORK DEVICES ......................5 TWISTED-PAIR DEVICES ..........................5 CABLING GUIDELINES ..........................5 RJ-45 MDI/MDI-X PORTS ON THE SWITCH THAT SUPPORT AUTOMATIC OUT CONFIGURATION SO YOU CAN USE STANDARD STRAIGHT THROUGH TWISTED PAIR CABLES TO CONNECT TO ANY OTHER ). - Page 5 3-4.4 CIST Ports ............................66 3-4.5 MSTI Ports ............................68 3-4.6 Bridge Status ............................70 3-4.7 Port Status ............................71 3-4.8 Port Statistics ............................72 3-5 IGMP S ............................73 NOOPING 3-5.1 Basic Configuration ..........................73 3-5.2 VLAN Configuration ..........................75 3-5.3 Port Group Filtering ..........................
- Page 6 3-14.9 DSCP Classification ........................163 3-14.10 QoS Control List Configuration ..................... 164 3-14.11 QCL Status ............................. 167 3-14.12 Storm Control ..........................169 3-14.13 WRED ............................170 3-15 ............................172 GENT 3-15.1 Collector ............................172 3-15.2 Sampler ............................174 3-16 E ...............................
- Page 7 5-5.1 Ping ..............................240 5-5.2 Ping6 ..............................241 5-5.3 VeriPHY ............................. 242 A. GLOSSARY OF WEB-BASED MANAGEMENT ..................243 A ..................................243 C..................................244 D ..................................244 E ..................................245 F ..................................246 H ..................................246 I ..................................246 L ..................................248 M ..................................
-
Page 9: Introduction
In this user’s manual, it will not only tell you how to install and connect your network system but configure and monitor the GTL-2880 by (RS-232) serial interface or through the web and Ethernet ports step-by-step. Many explanations in detail of hardware and software functions are shown as well as the examples of the operation for web-based interface. -
Page 10: Chapter 1 Operation Of Web-Based Management
MIBs status, each port activity, Spanning tree status, port aggregation status, multicast traffic, VLAN and priority status, even illegal access record and so on. he default values of the GTL-2880 are listed in the table below: IP Address 192.168.1.1 Subnet Mask 255.255.255.0... - Page 11 AS switch function can be enabled DHCP, so If you do not have DHCP server to provide ip addresses to the switch, the Switch default ip 192.168.1.1 Figure 1 The login page If you need to configuration the function or parameter then you can refer the detail in the User Guide.
- Page 12 GTL-2880 web help function:...
-
Page 13: Connecting Network Devices
The switch is designed to be connected to 10, 100 or CONNECTING 1000Mbps network cards in PCs and servers, as well as to other switches and hubs. It may also be NETWORK connected to remote devices using optional SFP DEVICES transceivers. -
Page 14: Network Wiring Connections
Step2. If the device is a network card and the switch is in the wiring closet, attach the other end of the cable segment to a modular wall outlet that is connected to the wiring closet. (See the section “Network Wiring Connections.”) Otherwise, attach the other end to an available port on the switch. -
Page 15: Chapter 2 System Configuration
2. Specify the contact information for the system administrator as well as the name and location of the switch. Also indicate the local time zone by configuring the appropriate offset. 3. Click Refresh Figure 2-1.1: System Information (GTL-2880 for example, others model the same) Parameter description:... - Page 16 Model name: The model name of this device. System description: As it is, this tells what this device is. Here, it is “20-Port 10/100/1000Base- T+ 4 TP / (100/1G) SFP Combo + 4 (1G/10G) SFP+ L2 Plus Managed Switch”.
-
Page 17: 2-1.2 Configuration
2-1.2 Configuration You can identify the system by configuring the contact information, name, and location of the switch. Web interface To configure System Information in the web interface: 1. Click System, System Information, Configuration. 2. Write System Contact, System Name, System Location information in this page. -
Page 18: 2-1.3 Cpu Load
2-1.3 CPU Load This page displays the CPU load, using an SVG graph. The load is measured as averaged over the last 100ms, 1sec and 10 seconds intervals. The last 120 samples are graphed, and the last numbers are displayed as text as well. In order to display the SVG graph, your browser must support the SVG format. -
Page 19: Time
Figure 2-2.1: The time configuration Parameter description: Clock Source: To click what clock source for the GTL-2880. You can select “Use local Settings” or “Use NTP Server” for GTL-2880 time clock source. Local Time: Show the current time of the system. - Page 20 The switch supports valid configurable day light saving time is –5 ~ +5 step one hour. The zero for this parameter means it need not have to adjust current time, equivalent to in-act daylight saving. You don’t have to set the starting/ending date as well.
-
Page 21: 2-2.2 Ntp
2-2.2 NTP NTP is Network Time Protocol and is used to sync the network time based Greenwich Mean Time (GMT). If use the NTP mode and select a built-in NTP time server or manually specify an user-defined NTP server as well as Time Zone, the switch will sync the time in a short after pressing <Apply>... -
Page 22: Account
2-3 Account In this function, only administrator can create, modify or delete the username and password. Administrator can modify other guest identities’ password without confirming the password but it is necessary to modify the administrator-equivalent identity. Guest-equivalent identity can modify his password only. Please note that you must confirm administrator/guest identity in the field of Authorization in advance before configuring the username and password. - Page 23 To type the password again. You must type the same password again in the field. Privilege Level : The privilege level of the user. The allowed range is 1 to 15. If the privilege level value is 15, it can access all groups, i.e. that is granted the fully control of the device.
-
Page 24: 2-3.2 Privilege Level
2-3.2 Privilege Level This page provides an overview of the privilege levels. The switch provides user set Account, Aggregation, Diagnostics, EEE, GARP, GVRP,IP, IPMC Snooping LACP LLDP LLDP MED MAC Table MRP MVR MVRP Maintenance Mirroring POE Ports Private VLANs QoS SMTP SNMP Security Spanning Tree System Trap Event VCL VLANs Voice VLAN Privilege Levels form 1 to 15 . - Page 25 Parameter description: Group Name The name identifying the privilege group. In most cases, a privilege level group consists of a single module (e.g. LACP, RSTP or QoS), but a few of them contains more than one. The following description defines these privilege level groups in details: System: Contact, Name, Location, Timezone, Log.
-
Page 26: 2-4.1 Ipv4
2-4 IP IP is an acronym for Internet Protocol. It is a protocol used for communicating data across an internet network. IP is a "best effort" system, which means that no packet of information sent over is assured to reach its destination in the same condition it was sent. Each device connected to a Local Area Network (LAN) or Wide Area Network (WAN) is given an Internet Protocol address, and this IP address is used to identify the device uniquely among all other devices connected to the extended network. - Page 27 Parameter description: DHCP Client : Enable the DHCP client by checking this box. If DHCP fails and the configured IP address is zero, DHCP will retry. If DHCP fails and the configured IP address is non-zero, DHCP will stop and the configured IP settings will be used. The DHCP client will announce the configured System Name as hostname to provide DNS lookup.
-
Page 28: 2-4.2 Ipv6
2-4.2 IPV6 This section describes how to configure the switch-managed IPv6 information. The Configured column is used to view or change the IPv6 configuration. And the Current column is used to show the active IPv6 configuration. Configure the switch-managed IPv6 information on this page. The Configured column is used to view or change the IPv6 configuration. -
Page 29: Syslog
2-5 Syslog The Syslog is a standard for logging program messages . It allows separation of the software that generates messages from the system that stores them and the software that reports and analyzes them. It can be used as well a generalized informational, analysis and debugging messages. -
Page 30: 2-5.2 Log
2-5.2 Log This section describes that display the system log information of the switch Web Interface To display the log configuration in the web interface: 1. Click Syslog, Log. 2. Display the log information. Figure2- 5.2: The System Log configuration Parameter description: Auto-refresh ... -
Page 31: 2-5.3 Detailed Log
2-5.3 Detailed Log This section describes that display the detailed log information of the switch Web Interface To display the detailed log configuration in the web interface: 1. Click Syslog, Detailed Log. 2. Display the log information. Figure2- 5.3: The Detailed System Log Information Parameter description: ... -
Page 32: Snmp
2-6 SNMP Any Network Management System (NMS) running the Simple Network Management Protocol (SNMP) can manage the Managed devices equipped with SNMP agent, provided that the Management Information Base (MIB) is installed correctly on the managed devices. The SNMP is a protocol that is used to govern the transfer of information between SNMP manager and agent and traverses the Object Identity (OID) of the management Information Base (MIB), described in the form of SMI syntax. -
Page 33: 2-6.2 Communities
2-6.2 Communities The function is used to configure SNMPv3 communities. The Community and UserName is unique. To create a new community account, please check <Add new community> button, and enter the account information then check <Save>. Max Group Number : 4. Web Interface To display the configure SNMP Communities in the web interface: 1. -
Page 34: 2-6.3 Users
2-6.3 Users The function is used to configure SNMPv3 user. The Entry index key is UserName. To create a new UserName account, please check <Add new user> button, and enter the user information then check <Save>. Max Group Number : 10. Web Interface To display the configure SNMP Users in the web interface: 1. - Page 35 protocol. SHA: An optional flag to indicate that this user uses SHA authentication protocol. The value of security level cannot be modified if entry already exists. That means must first ensure that the value is set correctly. Authentication Password A string identifying the authentication password phrase.
-
Page 36: 2-6.4 Groups
2-6.4 Groups The function is used to configure SNMPv3 group. The Entry index key are Security Model and Security Name. To create a new group account, please check <Add new group> button, and enter the group information then check <Save>. Max Group Number: v1: 2, v2: 2, v3:10. Web Interface To display the configure SNMP Groups in the web interface: 1. -
Page 37: 2-6.5 Views
2-6.5 Views The function is used to configure SNMPv3 view. The Entry index keys are OID Subtree and View Name. To create a new view account, please check <Add new view> button, and enter the view information then check <Save>. Max Group Number: 28. Configure SNMPv3 view table on this page. - Page 38 The OID defining the root of the subtree to add to the named view. The allowed OID length is 1 to 128. The allowed string content is digital number or asterisk(*). Save To click the Save icon to save the configuration to ROM.
-
Page 39: 2-6.6 Access
2-6.6 Access The function is used to configure SNMPv3 accesses. The Entry index key are Group Name, Security Model and Security level. To create a new access account, please check <Add new access> button, and enter the access information then check <Save>. Max Group Number : 14 Web Interface To display the configure SNMP Access in the web interface: 1. - Page 40 Auth, NoPriv: Authentication and no privacy. Auth, Priv: Authentication and privacy. Read View Name The name of the MIB view defining the MIB objects for which this request may request the current values. The allowed string length is 1 to 32, and the allowed content is ASCII characters from 33 to 126.
-
Page 41: 2-6.7 Tarp
2-6.7 Tarp The function is used to configure SNMP trap. To create a new trap account, please check <No number> button, and enter the trap information then check <Apply>. Max Group Number : 6. Web Interface To configure SNMP Trap setting: 1. - Page 42 Community / Security Name: The length of “Community / Security Name” string is restricted to 1-32. Security Level: Indicates what kind of message will send to Security Level. Possible modes are: Info: Send informations, warnings and errors. Warning: Send warnings and errors. Error: Send errors.
-
Page 43: Chapter 3. Configuration
Configuration Chapter 3. This chapter describes all of the basic network configuration tasks which includes the Ports, Layer 2 network protocol (e.g. VLANs, QoS, IGMP, ACLs and PoE etc.) and any setting of the Switch. 3-1 Port The section describes to configure the Port detail parameters of the switch. Others you could using the Port configure to enable or disable the Port of the switch. - Page 44 Parameter description: Port : This is the logical port number for this row. Link : The current link state is displayed graphically. Green indicates the link is up and red that it is down. Current Link Speed : ...
-
Page 45: 3-1.2 Port Description
3-1.2 Port Description The section describes to configure the Port’s alias or any descriptions for the Port Identity. It provides user to write down an alphanumeric string describing the full name and version identification for the system’s hardware type, software version, and networking application Web Interface To configure an Port Description in the web interface: 1. -
Page 46: 3-1.3 Traffic Overview
3-1.3 Traffic Overview The section describes to the Port statistics information and provides overview of general traffic statistics for all switch ports. Web Interface To Display the Port Statistics Overview in the web interface: 1. Click Configuration, Port, then Traffic Overview 2. -
Page 47: 3-1.4 Detailed Statistics
3-1.4 Detailed Statistics The section describes how to provide detailed traffic statistics for a specific switch port. Use the port select box to select which switch port details to display. The displayed counters are the totals for receive and transmit, the size counters for receive and transmit, and the error counters for receive and transmit. - Page 48 Rx and Tx Broadcast : The number of received and transmitted (good and bad) broadcast packets. Rx and Tx Pause : A count of the MAC Control frames received or transmitted on this port that have an opcode indicating a PAUSE operation. Receive and Transmit Size Counters The number of received and transmitted (good and bad) packets split into categories based on their respective frame sizes.
-
Page 49: 3-1.5 Qos Statistics
3-1.5 Qos Statistics The section describes that switch could display the QoS detailed Queuing counters for a specific switch port. for the different queues for all switch ports. Web Interface To Display the Queuing Counters in the web interface: 1. Click Configuration, Port, then QoS Statistics 2. -
Page 50: 3-1.6 Sfp Information
3-1.6 SFP Information The section describes that switch could display the SFP module detail information which you connect it to the switch. The information includes: Connector type, Fiber type, wavelength, banud rate and Vendor OUI etc. Web Interface To Display the SFP information in the web interface: 1. - Page 51 Show the serial number assigned by the manufacturer. Date Code: Show the date this SFP module was made. Temperature: Show the current temperature of SFP module. Vcc: Show the working DC voltage of SFP module. Mon1(Bias) mA: ...
-
Page 52: Acl
3-2 ACL The GTL-2880 switch access control list (ACL) is probably the most commonly used object in the IOS. It is used for packet filtering but also for selecting types of traffic to be analyzed, forwarded, or influenced in some way.The ACLs are divided into EtherTypes. IPv4, ARP protocol, MAC and VLAN parameters etc. - Page 53 Policy ID : Select the policy to apply to this port. The allowed values are 1 through 8. The default value is 1. Action : Select whether forwarding is permitted ("Permit") or denied ("Deny"). The default value is "Permit". Rate Limiter ID : ...
-
Page 54: 3-2.2 Rate Limiters
3-2.2 Rate Limiters The section describes how to configure the switch’s ACL Rate Limiter parameters. The Rate Limiter Level from 1 to 16 that allow user to set rate limiter value and units with pps or kbps. Web Interface To configure ACL Rate Limiter in the web interface: 1. -
Page 55: 3-2.3 Access Control List
3-2.3 Access Control List The section describes how to configure Access Control List rule. An Access Control List (ACL) is a sequential list of permit or deny conditions that apply to IP addresses, MAC addresses, or other more specific criteria. This switch tests ingress packets against the conditions in an ACL one by one. - Page 56 Parameter description: Ingress Port : Indicates the ingress port of the ACE. Possible values are: Any: The ACE will match any ingress port. Policy: The ACE will match ingress ports with a specific policy. Port: The ACE will match a specific ingress port. Frame Type : ...
- Page 57 buttons: : Inserts a new ACE before the current row. : Edits the ACE row. : Moves the ACE up the list. : Moves the ACE down the list. : Deletes the ACE. : The lowest plus sign adds a new entry at the bottom of the ACE listings. MAC Parameter: SMAC Filter ...
-
Page 58: 3-2.4 Acl Status
3-2.4 ACL Status The section describes how to shows the ACL status by different ACL users. Each row describes the ACE that is defined. It is a conflict if a specific ACE is not applied to the hardware due to hardware limitations. The maximum number of ACEs is 256 on each switch. Web Interface To display the ACL status in the web interface: 1. - Page 59 Mirror : Specify the mirror operation of this port. The allowed values are: Enabled: Frames received on the port are mirrored. Disabled: Frames received on the port are not mirrored. The default value is "Disabled". CPU : Forward packet that matched the specific ACE to CPU. CPU Once : ...
-
Page 60: Aggregation
3-3 Aggregation The Aggregation is used to configure the settings of Link Aggregation. You can bundle more than one port with the same speed, full duplex and the same MAC to be a single logical port, thus the logical port aggregates the bandwidth of these ports. This means you can apply your current Ethernet equipment’s to build the bandwidth aggregation. - Page 61 Parameter description: Hash Code Contributors Source MAC Address : The Source MAC address can be used to calculate the destination port for the frame. Check to enable the use of the Source MAC address, or uncheck to disable. By default, Source MAC Address is enabled. Destination MAC Address : ...
-
Page 62: 3-3.2 Lacp
3-3.2 LACP Ports using Link Aggregation Control Protocol (according to IEEE 802.3ad specification) as their trunking method can choose their unique LACP GroupID to form a logic “trunked port”. The benefit of using LACP is that a port makes an agreement with its peer port before it becomes a ready member of a “trunk group”... - Page 63 Parameter description: Port : The switch port number. LACP Enabled : Controls whether LACP is enabled on this switch port. LACP will form an aggregation when 2 or more ports are connected to the same partner. LACP can form max 12 LLAGs per switch and 2 GLAGs.
-
Page 64: 3-3.2.2 System Status
3-3.2.2 System Status This section describes that when you complete to set LACP function on the switch then it provides a status overview for all LACP instances Web Interface To display the LACP System status in the web interface: 1. Click Configuration, LACP, System Status 2. -
Page 65: 3-3.2.3 Port Status
3-3.2.3 Port Status This section describes that when you complete to set LACP function on the switch then it provides a Port Status overview for all LACP instances Web Interface To display the LACP Port status in the web interface: 1. - Page 66 LACP : 'Yes' means that LACP is enabled and the port link is up. 'No' means that LACP is not enabled or that the port link is down. 'Backup' means that the port could not join the aggregation group but will join if other port leaves. Meanwhile it's LACP status is disabled.
-
Page 67: 3-3.2.4 Port Statistics
3-3.2.4 Port Statistics This section describes that when you complete to set LACP function on the switch then it provides a Port Statistics overview for all LACP instances Web Interface To display the LACP Port status in the web interface: 1. -
Page 68: Spanning Tree
3-4 Spanning Tree The Spanning Tree Protocol (STP) can be used to detect and disable network loops, and to provide backup links between switches, bridges or routers. This allows the switch to interact with other bridging devices (that is, an STP-compliant switch, bridge or router) in your network to ensure that only one route exists between any two stations on the network, and provide backup links which automatically take over when a primary link goes down. - Page 69 Figure 3-4.1: The STP Bridge Configuration Parameter description: Basic Settings Protocol Version : The STP protocol version setting. Valid values are STP, RSTP and MSTP. Bridge Priority : Controls the bridge priority. Lower numeric values have better priority. The bridge priority plus the MSTI instance number, concatenated with the 6-byte MAC address of the switch forms a Bridge Identifier.
- Page 70 Edge Port BPDU Guard : Control whether a port explicitly configured as Edge will disable itself upon reception of a BPDU. The port will enter the error-disabled state, and will be removed from the active topology. Port Error Recovery : ...
-
Page 71: 2-4.2 Msti Mapping
2-4.2 MSTI Mapping When you implement an Spanning Tree protocol on the switch that the bridge instance. The CIST is not available for explicit mapping, as it will receive the VLANs not explicitly mapped. Due to the reason that you need to set the list of VLANs mapped to the MSTI. The VLANs must be separated with comma and/or space. - Page 72 MSTI Mapping MSTI : The bridge instance. The CIST is not available for explicit mapping, as it will receive the VLANs not explicitly mapped. VLANs Mapped : The list of VLANs mapped to the MSTI. The VLANs must be separated with comma and/or space.
-
Page 73: 3-4.3 Msti Priorities
3-4.3 MSTI Priorities When you implement an Spanning Tree protocol on the switch that the bridge instance. The CIST is the default instance which is always active. For controls the bridge priority. Lower numeric values have better priority. The bridge priority plus the MSTI instance number, concatenated with the 6-byte MAC address of the switch forms a Bridege Identifier The section describes it allows the user to inspect the current STP MSTI bridge instance priority configurations, and possibly change them as well. -
Page 74: 3-4.4 Cist Ports
3-4.4 CIST Ports When you implement an Spanning Tree protocol on the switch that the bridge instance. You need to configure the CIST Ports. The section describes it allows the user to inspect the to inspect the current STP CIST port configurations, and possibly change them as well. Web Interface To configure the Spanning Tree CIST Ports parameters in the web interface: 1. - Page 75 cost ports are chosen as forwarding ports in favour of higher path cost ports. Valid values are in the range 1 to 200000000. Priority : Controls the port priority. This can be used to control priority of ports having identical port cost.
-
Page 76: 3-4.5 Msti Ports
3-4.5 MSTI Ports The section describes it allows the user to inspect the current STP MSTI port configurations, and possibly change them as well. An MSTI port is a virtual port, which is instantiated separately for each active CIST (physical) port for each MSTI instance configured on and applicable to the port. - Page 77 Port : The switch port number of the corresponding STP CIST (and MSTI) port. Path Cost : Controls the path cost incurred by the port. The Auto setting will set the path cost as appropriate by the physical link speed, using the 802.1D recommended values.
-
Page 78: 3-4.6 Bridge Status
3-4.6 Bridge Status After you complete the MSTI Port configuration the you could to ask the switch display the Bridge Status. The Section provides a status overview of all STP bridge instances. The displayed table contains a row for each STP bridge instance, where the column displays the following information: Web Interface To display the STP Bridges status in the web interface:... -
Page 79: 3-4.7 Port Status
3-4.7 Port Status After you complete the STP configuration the you could to ask the switch display the STP Port Status. The Section provides you to ask switch to display the STP CIST port status for physical ports of the currently selected switch.: Web Interface To display the STP Port status in the web interface: 1. -
Page 80: 3-4.8 Port Statistics
3-4.8 Port Statistics After you complete the STP configuration then you could to let the switch display the STP Statistics. The Section provides you to ask switch to display the STP Statistics detail counters of bridge ports in the currently selected switch. Web Interface To display the STP Port status in the web interface: 1. -
Page 81: Igmp Snooping
3-5 IGMP Snooping The function, is used to establish the multicast groups to forward the multicast packet to the member ports, and, in nature, avoids wasting the bandwidth while IP multicast packets are running over the network. This is because a switch that does not support IGMP or IGMP Snooping can not tell the multicast packet from the broadcast packet, so it can only treat them all as the broadcast packet. - Page 82 Parameter description: Snooping Enabled: Enable the Global IGMP Snooping. Unregistered IPMCv4 Flooding enabled : Enable unregistered IPMCv4 traffic flooding. IGMP SSM Range : SSM (Source-Specific Multicast) Range allows the SSM-aware hosts and routers run the SSM service model for the groups in the address range. Format: (IP address/ sub mask) Proxy Enabled : ...
-
Page 83: 3-5.2 Vlan Configuration
3-5.2 VLAN Configuration The section describes the VLAN configuration setting process integrated with IGMP Snooping function. For Each setting page shows up to 99 entries from the VLAN table, default being 20, selected through the "entries per page" input field. When first visited, the web page will show the first 20 entries from the beginning of the VLAN Table. - Page 84 inserted into the periodic General Queries. The allowed range is 0 to 31744 in tenths of seconds; default query response interval is 100 in tenths of seconds (10 seconds). LLQI (LMQI for IGMP) : Last Member Query Interval. The Last Member Query Time is the time value represented by the Last Member Query Interval, multiplied by the Last Member Query Count.
-
Page 85: 3-5.3 Port Group Filtering
3-5.3 Port Group Filtering The section describes how to set the IGMP Port Group Filtering? With the IGMP filtering feature, an user can exert this type of control. In some network Application environments, as like the metropolitan or multiple-dwelling unit (MDU) installations, an user might want to control the multicast groups to which a user on a switch port can belong. - Page 86 Filtering Groups : The IP Multicast Group that will be filtered. Buttons: Save – Click to save changes. Reset- Click to undo any changes made locally and revert to previously saved values.
-
Page 87: 3-5.4 Status
3-5.4 Status After you complete the IGMP Snooping configuration, then you could to let the switch display the IGMP Snooping Status. The Section provides you to let switch to display the IGMP Snooping detail status. Web Interface To display the IGMP Snooping status in the web interface: 1. - Page 88 V3 Reports Received : The number of Received V3 Reports. V2 Leaves Received : The number of Received V2 Leaves. Auto-refresh To evoke the auto-refresh icon then the device will refresh the log automatically. Upper right icon (Refresh, clear) ...
-
Page 89: 3-5.5 Group Information
3-5.5 Group Information After you complete to set the IGMP Snooping function then you could let the switch to display the IGMP Snooping Group Information. Entries in the IGMP Group Table are shown on this page. The IGMP Group Table is sorted first by VLAN ID, and then by group. The will use the last entry of the currently displayed table as a basis for the next lookup. -
Page 90: 3-5.6 Ipv4 Ssm Information
3-5.6 IPv4 SSM information Source Specific Multicast (SSM) is a datagram delivery model that best supports one-to-many applications, also known as broadcast applications. SSM is a core network technology of IP multicast targeted for audio and video broadcast application environments. For the SSM delivery mode, an IP multicast receiver host must use IGMP Version 3 (IGMPv3) to subscribe to channel (S, G). - Page 91 Group address of the group displayed. Port : Switch port number. Mode : Indicates the filtering mode maintained per (VLAN ID, port number, Group Address) basis. It can be either Include or Exclude. Source Address : IP Address of the source. Currently, system limits the total number of IP source addresses for filtering to be 128.
-
Page 92: Mld Snooping
3-6 MLD Snooping Curiously enough, a network node that acts as a source of IPv6 multicast traffic is only an indirect participant in MLD snooping—it just provides multicast traffic, and MLD doesn’t interact with it. (Note, however, that in an application like desktop conferencing a network node may act as both a source and an MLD host;... -
Page 93: Router Port
Parameter description: Snooping Enabled : Enable the Global MLD Snooping. Unregistered IPMCv6 Flooding enabled : Enable unregistered IPMCv6 traffic flooding. Please note that disabling unregistered IPMCv6 traffic flooding may lead to failure of Neighbor Discovery. MLD SSM Range : ... -
Page 94: 3-6.2 Vlan Configuration
3-6.2 VLAN Configuration When MLD snooping is enabled on a VLAN, the switch acts to minimize unnecessary multicast traffic. If the switch receives multicast traffic destined for a given multicast address, it forwards that traffic only to ports on the VLAN that have MLD hosts for that address. It drops that traffic for ports on the VLAN that have no MLD hosts The will use the last entry of the currently displayed entry as a basis for the next lookup. - Page 95 Last Listener Query Interval. The Last Listener Query Interval is the Maximum Response Delay used to calculate the Maximum Response Code inserted into Multicast Address Specific Queries sent in response to Version 1 Multicast Listener Done messages. It is also the Maximum Response Delay used to calculate the Maximum Response Code inserted into Multicast Address and Source Specific Query messages.
-
Page 96: 3-6.3 Port Group Filtering
3-6.3 Port Group Filtering The section describes that you could to set the Port Group Filtering in the MLD Snooping function. On the UI that you could add new filtering group and safety policy. Web Interface To configure the MLD Snooping Port Group Configuration in the web interface: 1. -
Page 97: 3-6.4 Status
3-6.4 Status The section describes when you complete the MLD Snooping and how to display the MLD Snooping Status and detail information. It will help you to find out the detail information of MLD Snooping status. Web Interface To display the MLD Snooping Status in the web interface: 1. - Page 98 The number of Received V1 Reports. V2 Reports Received : The number of Received V2 Reports. V1 Leaves Received : The number of Received V1 Leaves. Auto-refresh To evoke the auto-refresh icon then the device will refresh the log automatically. Upper right icon (Refresh, <<, >>...
-
Page 99: 3-6.5 Group Information
3-6.5 Group Information The section describes user could set the MLD Snooping Groups Information. The "Start from VLAN", and "group" input fields allow the user to select the starting point in the MLD Group Table Each page shows up to 99 entries from the MLD Group table, default being 20, selected through the "entries per page"... - Page 100 Auto-refresh : To evoke the auto-refresh icon then the device will refresh the log automatically. Upper right icon (Refresh, <<, >> ): You can click them for refresh the IGMP Group Status by manual, others for next/up page or entry..
-
Page 101: 3-6.6 Ipv6 Ssm Information
3-6.6 IPv6 SSM Information The section describes the user to configure the Entries in the MLDv2 Information Table are shown on this page. The MLDv2 Information Table is sorted first by VLAN ID, then by group, and then by Port No. Diffrent source addresses belong to the same group are treated as single entry. -
Page 102: Mvr
3-7 MVR The MVR feature enables multicast traffic forwarding on the Multicast VLAN. In a multicast television application, a PC or a television with a set-top box can receive the multicast stream. Multiple set-top boxes or PCs can be connected to one subscriber port, which is a switch port configured as an MVR receiver port. - Page 103 Parameter description: MVR Mode : Enable/Disable the Global MVR. VLAN ID : Specify the Multicast VLAN ID. Mode : Enable MVR on the port. Type : Specify the MVR port type on the port. Immediate Leave : ...
-
Page 104: 3-7.2 Groups Information
3-7.2 Groups Information The section describes user could display the MVR Groups detail information on the switch. Entries in the MVR Group Table are shown on this page. The MVR Group Table is sorted first by VLAN ID, and then by group Web Interface To display the MVR Groups Information in the web interface: 1. -
Page 105: 3-7.3 Statistics
3-7.3 Statistics The section describes the switch will display the MVR detail Statistics after you had configured MVR on the switch. It provides the detail MVR Statistics Information Web Interface To display the MVR Statistics Information in the web interface: 1. -
Page 106: Lldp
3-8 LLDP The switch supports the LLDP. For current information on your switch model, The Link Layer Discovery Protocol (LLDP) provides a standards-based method for enabling switches to advertise themselves to adjacent devices and to learn about adjacent LLDP devices. The Link Layer Discovery Protocol (LLDP) is a vendor-neutral Link Layer protocol in the Internet Protocol Suite used by network devices for advertising their identity, capabilities, and neighbors on a IEEE 802 local area network, principally wired Ethernet. - Page 107 LLDP Parameters Tx Interval : The switch periodically transmits LLDP frames to its neighbours for having the network discovery information up-to-date. The interval between each LLDP frame is determined by the Tx Interval value. Valid values are restricted to 5 - 32768 seconds. Tx Hold : ...
- Page 108 capabilities that are not part of the LLDP. These capabilities are shown as "others" in the LLDP neighbors’ table. If all ports have CDP awareness disabled the switch forwards CDP frames received from neighbor devices. If at least one port has CDP awareness enabled all CDP frames are terminated by the switch.
-
Page 109: 3-8.2 Lldp Neighbours
3-8.2 LLDP Neighbours This page provides a status overview for all LLDP neighbours. The displayed table contains a row for each port on which an LLDP neighbour is detected. The columns hold the following information: Web Interface To show LLDP neighbours: 1. -
Page 110: System Description
When a capability is enabled, the capability is followed by (+). If the capability is disabled, the capability is followed by (-). System Description : System Description is the port description advertised by the neighbour unit. Management Address : ... -
Page 111: 3-8.3 Lldp-Med Configuration
3-8.3 LLDP-MED Configuration Media Endpoint Discovery is an enhancement of LLDP, known as LLDP-MED that provides the following facilities: Auto-discovery of LAN policies (such as VLAN, Layer 2 Priority and Differentiated services (Diffserv) settings) enabling plug and play networking. Device location discovery to allow creation of location databases and, in the case of Voice over Internet Protocol (VoIP), Enhanced 911 services. - Page 112 Fast start repeat count Rapid startup and Emergency Call Service Location Identification Discovery of endpoints is a critically important aspect of VoIP systems in general. In addition, it is best to advertise only those pieces of information which are specifically relevant to particular endpoint types (for example only advertise the voice network policy to permitted voice-capable devices), both in order to conserve the limited LLDPU space and to reduce security and system integrity issues that can come with inappropriate knowledge of the network policy.
- Page 113 Civic Address Location IETF Geopriv Civic Address based Location Configuration Information (Civic Address LCI). Country code : The two-letter ISO 3166 country code in capital ASCII letters - Example: DK, DE or US. State : National subdivisions (state, canton, region, province, prefecture). County : ...
- Page 114 Place type : Place type - Example: Office. Postal community name : Postal community name - Example: Leonia. P.O. Box : Post office box (P.O. BOX) - Example: 12345. Additional code : Additional code - Example: 1320300003. Emergency Call Service: ...
- Page 115 ID for the policy. This is auto generated and shall be used when selecting the polices that shall be mapped to the specific ports. Application Type : Intended use of the application types: 1. Voice - for use by dedicated IP Telephony handsets and other similar appliances supporting interactive voice services.
- Page 116 Click to add a new policy. Specify the Application type, Tag, VLAN ID, L2 Priority and DSCP for the new policy. Click "Save". Port Policies Configuration : Every port may advertise a unique set of network policies or different attributes for the same network policies, based on the authenticated user identity or port configuration.
-
Page 117: 3-8.4 Lldp-Med Neighbours
3-8.4 LLDP-MED Neighbours This page provides a status overview of all LLDP-MED neighbours. The displayed table contains a row for each port on which an LLDP neighbour is detected. This function applies to VoIP devices which support LLDP-MED. The columns hold the following information: Web Interface To show LLDP-MED neighbor: 1.Click LLDP-MED Neighbor... - Page 118 LLDP-MED Generic Endpoint (Class I) : The LLDP-MED Generic Endpoint (Class I) definition is applicable to all endpoint products that require the base LLDP discovery services defined in TIA-1057, however do not support IP media or act as an end-user communication appliance. Such devices may include (but are not limited to) IP Communication Controllers, other communication related servers, or any device requiring basic services as defined in TIA-1057.
- Page 119 as PCs or laptops. 6. Video Conferencing - for use by dedicated Video Conferencing equipment and other similar appliances supporting real-time interactive video/audio services. 7. Streaming Video - for use by broadcast or multicast based video content distribution and other similar applications supporting streaming video services that require specific network policy treatment.
-
Page 120: 3-8.5 Eee
3-8.5 EEE By using EEE power savings can be achieved at the expense of traffic latency. This latency occurs due to that the circuits EEE turn off to save power, need time to boot up before sending traffic over the link. This time is called "wakeup time". To achieve minimal latency, devices can use LLDP to exchange information about their respective tx and rx "wakeup time ", as a way to agree upon the minimum wakeup time they need. - Page 121 Resolved Tx Tw : The resolved Tx Tw for this link. Note : NOT the link partner The resolved value that is the actual "tx wakeup time " used for this link (based on EEE information exchanged via LLDP). Resolved Rx Tw : ...
-
Page 122: 3-8.6 Port Statistics
3-8.6 Port Statistics Two types of counters are shown. Global counters are counters that refer to the whole switch, while local counters refer to per port counters for the currently selected switch Web Interface To show LLDP Statistics: 1. Click LLDP, than click Port Statistics to show LLDP counters 2. - Page 123 The port on which LLDP frames are received or transmitted. Tx Frames : The number of LLDP frames transmitted on the port. Rx Frames : The number of LLDP frames received on the port. Rx Errors : The number of received LLDP frames containing some kind of error.
-
Page 124: Filtering Data Base
3- 9 Filtering Data Base Filtering Data Base Configuration gathers many functions, including MAC Table Information, Static MAC Learning, which cannot be categorized to some function type. MAC table Switching of frames is based upon the DMAC address contained in the frame. The switch builds up a table that maps MAC addresses to switch ports for knowing which ports the frames should go to (based upon the DMAC address in the frame). -
Page 125: Aging Configuration
Parameter description: Aging Configuration : By default, dynamic entries are removed from the MAC table after 300 seconds. This removal is also called aging. Configure aging time by entering a value here in seconds; for example, Age time seconds. The allowed range is 10 to 1000000 seconds. -
Page 126: 3- 9.2 Dynamic Mac Table
3- 9.2 Dynamic MAC Table Entries in the MAC Table are shown on this page. The MAC Table contains up to 8192 entries, and is sorted first by VLAN ID, then by MAC address. Web Interface To Display MAC Address Table in the web interface: 1. -
Page 127: Vlan
3-10 VLAN To assign a specific VLAN for management purpose. The management VLAN is used to establish an IP connection to the switch from a workstation connected to a port in the VLAN. This connection supports a VSM, SNMP, and Telnet session. By default, the active management VLAN is VLAN 1, but you can designate any VLAN as the management VLAN using the Management VLAN window. - Page 128 A row of check boxes for each port is displayed for each VLAN ID. To include a port in a VLAN, check the box. To remove or exclude the port from the VLAN, make sure the box is unchecked. By default, no ports are members, and all boxes are unchecked. Adding a New VLAN : ...
-
Page 129: 3-10.2 Ports
3-10.2 Ports User can configure all parameter to each port in VLAN Port Setting. These parameter involved two parts, Ingress rule and Egress rule. The function of Port Type, Ingress Filtering, Frame Type, and PVID affect Ingress process. Furthermore, Port Type, Egress Rule, and PVID affect Egress process. -
Page 130: Ingress Filtering
Ingress action Egress action Unaware when the port received untagged frames, an The TPID of frame untagged frame obtain a tag (based on PVID) transmitted by The fuction of and is forwarded. Unaware port will be Unaware can when the port received tagged frames, if an set to 0x8100. - Page 131 untagged frames will be transmitted. PVID : Configures the Port VLAN identifier. The allowed values are 1 through 4094. The default value is 1. When the port received a untagged frame, the port will give a tag to it based on the value of PVID, and the frame become tagged frame.
-
Page 132: 3-10.3 Switch Status
3-10.3 Switch Status The function Switch Status gathers the information of all VLAN status and reports it by the order of Static NAS MVRP MVP Voice VLAN MSTP GVRP Combined. Web Interface To Display VLAN membership status n the web interface: 1. -
Page 133: 3-10.4 Port Status
3-10.4 Port Status The function Port Status gathers the information of all VLAN status and reports it by the order of Static NAS MVRP MVP Voice VLAN MSTP GVRP Combined. Web Interface To Display VLAN Port Status n the web interface: 1. - Page 134 Conflicts : Shows status of Conflicts whether exists or not. When a Volatile VLAN User requests to set VLAN membership or VLAN port configuration, the following conflicts can occur: Functional Conflicts between features. Conflicts due to hardware limitation. Direct conflict between user modules. Auto-refresh : ...
-
Page 135: 3-10.5 Private Vlans
3-10.5 Private VLANs In a private VLAN, communication between ports in that private VLAN is not permitted. A VLAN can be configured as a private VLAN. 3-10.5.1 Private VLANs Membership The Private VLAN membership configurations for the switch can be monitored and modified here. -
Page 136: 3-10.5.2 Port Isolation
3-10.5.2 Port Isolation Port Isolation provides for an apparatus and method to isolate ports on layer 2 switches on the same VLAN to restrict traffic flow. The apparatus comprises a switch having said plurality of ports, each port configured as a protected port or a non-protected port. An address table memory stores an address table having a destination address and port number pair. -
Page 137: 3-10.6 Mac-Based Vlan
3-10.6 MAC-based VLAN MAC address-based VLAN decides the VLAN for forwarding an untagged frame based on the source MAC address of the frame. A most common way of grouping VLAN members is by port, hence the name port-based VLAN. Typically, the device adds the same VLAN tag to untagged packets that are received through the same port. - Page 138 MAC Address : Indicates the MAC address. VLAN ID : Indicates the VLAN ID. Port Members : A row of check boxes for each port is displayed for each MAC-based VLAN entry. To include a port in a MAC-based VLAN, check the box. To remove or exclude the port from the MAC- based VLAN, make sure the box is unchecked.
-
Page 139: 3-10.6.2 Status
3-10.6.2 Status section This shows MAC-based VLAN entries configured by various MAC-based VLAN users. Currently we support following VLAN User types: NAS : NAS provides port-based authentication, which involves communications between a Supplicant, Authenticator, and an Authentication Server. Web Interface To Display MAC-based VLAN configured in the web interface: 1. -
Page 140: 3-10.7 Protocol -Based Vlan
3-10.7 Protocol -based VLAN This section describe Protocol -based VLAN, The Switch support Protocol include Ethernet LLC SNAP Protocol, The Logical Link Control (LLC) data communication protocol layer is the upper sub-layer of the Data Link Layer (which is itself layer 2, just above the Physical Layer) in the seven- layer OSI reference model. - Page 141 Parameter description: Delete : To delete a Protocol to Group Name map entry, check this box. The entry will be deleted on the switch during the next Save. Frame Type : Frame Type can have one of the following values: Ethernet SNAP On changing the Frame type field, valid value of the...
-
Page 142: 3-10.7.2 Group To Vlan
3-10.7.2 Group to VLAN This section allows you to map a already configured Group Name to a VLAN for the selected switch. Web Interface To Display Group Name to VLAN mapping table configured in the web interface: 1. Click Group Name VLAN configuration and add new entry. 2. - Page 143 Auto-refresh : To evoke the auto-refresh icon then the device will refresh the information automatically. Upper right icon (Refresh): You can click them for refresh the Protocol Group Mapping information by manual.
-
Page 144: Voice Vlan
3-11 Voice VLAN Voice VLAN is VLAN configured specially for voice traffic. By adding the ports with voice devices attached to voice VLAN, we can perform QoS-related configuration for voice data, ensuring the transmission priority of voice traffic and voice quality. 3-11.1 Configuration The Voice VLAN feature enables voice traffic forwarding on the Voice VLAN, then the switch can classify and schedule network traffic. -
Page 145: Aging Time
Parameter description: Mode : Indicates the Voice VLAN mode operation. We must disable MSTP feature before we enable Voice VLAN. It can avoid the conflict of ingress filtering. Possible modes are: Enabled: Enable Voice VLAN mode operation. Disabled: Disable Voice VLAN mode operation. VLAN ID : ... -
Page 146: 3-11.2 Oui
3-11.2 OUI The section describes to Configure VOICE VLAN OUI table . The maximum entry number is 16. Modifying the OUI table will restart auto detection of OUI process. Web Interface To configure Voice VLAN OUI Table in the web interface: 1. -
Page 147: Garp
3-12 GARP The Generic Attribute Registration Protocol (GARP) provides a generic framework whereby devices in a bridged LAN, e.g. end stations and switches, can register and de-register attribute values, such as VLAN Identifiers, with each other. In doing so, the attributes are propagated to devices in the bridged LAN, and these devices form a ¡°reachability¡±... - Page 148 Attribute Type GARP Applicant Timer Values : To set the GARP join timer, leave timer and .leave all timers, units is Micro-second. Three different timers can be configured on this page: Join Timer :The default value for Join timer is 200ms. Leave Timer : The range of values for Leave Time is 600-1000ms.
-
Page 149: 3-12.2 Statistics
3-12.2 Statistics The section describes to port statistics of GARP for all switch ports.The port statistics relate to the currently selected unit, as reflected by the page header. Web Interface To display GARP Port statistics in the web interface: 1. Click GARP statistics. 2. -
Page 150: Gvrp
3-13 GVRP GVRP is an application based on Generic Attribute Registration Protocol (GARP), mainly used to automatically and dynamically maintain the group membership information of the VLANs. The GVRP offers the function providing the VLAN registration service through a GARP application. - Page 151 Parameter description: GVRP Mode : GVRP Mode is a global setting, to enable the GVRP globally select 'Enable' from menu and to disable GVRP globally select 'Disable'. Port : The Port coulmn shows the list of ports for which you can configure per port GVRP settings. There are three configuration settings which can be configured on per port bases.
-
Page 152: 3-13.2 Statistics
3-13.2 Statistics The section describes to shows the basic GVRP Port statistics for all switch ports. The statistics relate to the currently selected unit, as reflected by the page header. Web Interface To display GVRP Port statistics in the web interface: 1. -
Page 153: Qos
3-14 QoS The switch support four QoS queues per port with strict or weighted fair queuing scheduling. It supports QoS Control Lists (QCL) for advance programmable QoS classification, based on IEEE 802.1p, Ethertype, VID, IPv4/IPv6 DSCP and UDP/TCP ports and ranges. High flexibility in the classification of incoming frames to a QoS class. - Page 154 Parameter description: Port : The port number for which the configuration below applies. QoS class : Controls the default QoS class, i.e., the QoS class for frames not classified in any other way. There is a one to one mapping between QoS class, queue and priority. A QoS class of 0 (zero) has the lowest priority.
-
Page 155: 3-14.2 Port Policing
3-14.2 Port Policing This section provides an overview of f QoS Ingress Port Policers for all switch ports The Port Policing is useful in constraining traffic flows and marking frames above specific rates. Policing is primarily useful for data flows and voice or video flows because voice and video usually maintains a steady rate of traffic Web Interface To display the QoS Port Schedulers in the web interface:... - Page 156 values.
-
Page 157: 3-14.3 Port Scheduler
3-14.3 Port Scheduler This section provides an overview of QoS Egress Port Schedulers for all switch ports. and the ports belong to the currently selected unit, as reflected by the page header. Web Interface To display the QoS Port Schedulers in the web interface: 1. - Page 158 If you select the scheduler mode with wighted then the screen will change as the figure. Parameter description: Port : The logical port for the settings contained in the same row. Click on the port number in order to configure the schedulers. Mode : ...
- Page 159 Shows the weight in percent for this queue. This parameter is only shown if "Scheduler Mode" is set to "Weighted" Port Shaper Enable : Controls whether the port shaper is enabled for this switch port. Port Shaper Rate : ...
-
Page 160: 3-14.4 Port Shaping
3-14.4 Port Shaping This section provides an overview of QoS Egress Port Shaping for all switch ports. Others the user could get all detail information ot the ports belong to the currently selected unit, as reflected by the page header. Web Interface To display the QoS Port Shapers in the web interface: 1. - Page 161 If you select the scheduler mode with wighted then the screen will change as the figure. Parameter description: Port : The logical port for the settings contained in the same row. Click on the port number in order to configure the shapers. Shapers (Qn) : ...
- Page 162 Controls the weight for this queue. The default value is "17". This value is restricted to 1-100. This parameter is only shown if "Scheduler Mode" is set to "Weighted". Queue Scheduler Percent : Shows the weight in percent for this queue. This parameter is only shown if "Scheduler Mode"...
-
Page 163: 3-14.5 Port Tag Remarking
3-14.5 Port Tag Remarking The Section provides user to get an overview of QoS Egress Port Tag Remarking for all switch ports. Others the ports belong to the currently selected unit, as reflected by the page header. . Web Interface To display the QoS Port Tag Remarking in the web interface: 1. - Page 164 Save – Click to save changes. Reset- Click to undo any changes made locally and revert to previously saved values. Cancel – Click to cancel the changes.
-
Page 165: 3-14.6 Port Dscp
3-14.6 Port DSCP The section will teach user to set the QoS Port DSCP configuration that was allowed you to configure the basic QoS Port DSCP Configuration settings for all switch ports. Others the settings relate to the currently selected unit, as reflected by the page header. Web Interface To configure the QoS Port DSCP parameters in the web interface: 1. - Page 166 DSCP=0: Classify if incoming (or translated if enabled) DSCP is 0. Selected: Classify only selected DSCP for which classification is enabled as specified in DSCP Translation window for the specific DSCP. All: Classify all DSCP. Egress : ...
-
Page 167: 3-14.7 Dscp-Based Qos
3-14.7 DSCP-Based QoS The section will teach user to configure the DSCP-Based QoS mode that This page allows you to configure the basic QoS DSCP based QoS Ingress Classification settings for all switches. Web Interface To configure the DSCP –Based QoS Ingress Classification parameters in the web interface: 1. - Page 168 Parameter description: DSCP : Maximum number of support ed DSCP values are 64. Trust : Click to check if the DSCP value is trusted. QoS Class : QoS Class value can be any of (0-7) DPL : Drop Precedence Level (0-3) ...
-
Page 169: 3-14.8 Dscp Translation
3-14.8 DSCP Translation The section describes the swtich allows you to configure the basic QoS DSCP Translation settings for all switches. DSCP translation can be done in Ingress or Egress. Web Interface To configure the DSCP Translation parameters in the web interface: 1. - Page 170 Parameter description: DSCP : Maximum number of supported DSCP values are 64 and valid DSCP value ranges from 0 to Ingress : Ingress side DSCP can be first translated to new DSCP before using the DSCP for QoS class and DPL map.
-
Page 171: 3-14.9 Dscp Classification
3-14.9 DSCP Classification The section describes to teach user to configure and allows you to map DSCP value to a QoS Class and DPL value. Others the settings relate to the currently selected unit, as reflected by the page header. Web Interface To configure the DSCP Classification parameters in the web interface: 1.Click Configuration, QoS, DSCP Translation... -
Page 172: 3-14.10 Qos Control List Configuration
3-14.10 QoS Control List Configuration The section shows the QoS Control List(QCL), which is made up of the QCEs. Each row describes a QCE that is defined. The maximum number of QCEs is 256 on each switch. Click on the lowest plus sign to add a new QCE to the list. Web Interface To configure the QoS Control List parameters in the web interface: 1. - Page 173 Specify the type of Destination MAC addresses for incoming frame. Possible values are: Any: All types of Destination MAC addresses are allowed. Unicast: Only Unicast MAC addresses are allowed. Multicast: Only Multicast MAC addresses are allowed. Broadcast: Only Broadcast MAC addresses are allowedd. The default value is 'Any'.
- Page 174 broadcast(BC) or 'Any' Frame Type Frame Type can have any of the following values 1. Any 2. Ethernet 3. LLC 4. SNAP 5. IPv4 6. IPv6 NOTE: All frame types are explained below: 1. Any : Allow all types of frames. 2.
-
Page 175: 3-14.11 Qcl Status
3-14.11 QCL Status The section will let you know how to configure and shows the QCL status by different QCL users. Each row describes the QCE that is defined. It is a conflict if a specific QCE is not applied to the hardware due to hardware limitations. The maximum number of QCEs is 256 on each switch. - Page 176 under DSCP column. Conflict : Displays QCE status. It may happen that resources required to add a QCE may not available, in that case it shows conflict status as 'Yes', otherwise it is always 'No'.Please note that conflict can be resolved by releaseing the resource required by the QCE and pressing 'Refresh' button.
-
Page 177: 3-14.12 Storm Control
3-14.12 Storm Control The section allows user to configure the Storm control for the switch. There is a unicast storm rate control, multicast storm rate control, and a broadcast storm rate control. These only affect flooded frames, i.e. frames with a (VLAN ID, DMAC) pair not present on the MAC Address table. -
Page 178: 3-14.13 Wred
3-14.13 WRED The section allows user to configure the WRED function for the switch. This page allows you to configure the Random Early Detection (RED) settings for queue 0 to 5. RED cannot be applied to queue 6 and 7. Through different RED configuration for the queues ( ) it is possible to obtain QoS classes... - Page 179 Controls the drop probability for frames marked with Drop Precedence Level 3 when the average queue filling level is 100%. This value is restricted to 0-100. NOTE: RED Drop Probability Function The following illustration shows the drop probability function with associated parameters.
-
Page 180: S-Flow Agent
3-15 s-Flow Agent The sFlow Collector configuration for the switch can be monitored and modified here. Up to 1 Collector is supported. This page allows for configuring sFlow collector IP type, sFlow collector IP Address,Port Number, for each sFlow Collector 3-15.1 Collector The "Current "... - Page 181 The value accepted is within the range of 1-65535. But an appropriate port number not used by other protocols need to be configured. By default, the port's number is 6343 Time out : It is the duration during which the collector receives samples, once it is expired the sampler stops sending the samples.
-
Page 182: 3-15.2 Sampler
3-15.2 Sampler The section display the sFlow sampler what you set or you can edit it for your requirement. That will help user based on a defined sampling rate, an average of 1 out of N packets/operations is randomly sampled. This type of sampling does not provide a 100% accurate result, but it does provide a result with quantifiable accuracy Web Interface To configure the sFlow Agent in the web interface:... -
Page 183: Sampling Rate
Configured sFlow instance for the port number. Sampler Type : Configured sampler type on the port and could be any of the types: None, Rx, Tx or All. You can scroll to choice one for your sampler type. By default, The value is “None”. Sampling Rate : ... -
Page 184: Easy Port
3-16 Easy Port Easy Port provide a convenient way to save and share common configurations. You can use it to enable features and settings based on the location of a switch in the network and for mass configuration deployments across the network. You could easy to implement included Voice IP phone, Wireless Access Point and IP Camera…etc. - Page 185 To scroll to enable or disable the Port Security function on the Port. If you turn on the function then you need to set Port Security limit to allow how many device can access the port (via MAC address). Port Security Action : ...
-
Page 186: Mirroring
3-17. Mirroring You can mirror traffic from any source port to a target port for real-time analysis. You can then attach a logic analyzer or RMON probe to the target port and study the traffic crossing the source port in a completely unobtrusive manner. Mirror Configuration is to monitor the traffic of the network. - Page 187 Mirror Port Configuration The following table is used for Rx and Tx enabling. Port : The logical port for the settings contained in the same row. Mode : Select mirror mode. Rx only Frames received on this port are mirrored on the mirror port. Frames transmitted are not mirrored.
-
Page 188: Trap Event Severity
3-18. Trap Event Severity The function is used to set an Alarm trap and get the Event log. The Trap Events Configuration function is used to enable the switch to send out the trap information while pre-defined trap events occurred. Web Interface To configure the Trap Event Severity Configuration in the web interface: 1. -
Page 189: Smtp Configuration
3-19. SMTP Configuration The function is used to set an Alarm trap when the switch alarm then you could set the SMTP server to send you the alarm mail. Web Interface To configure the SMTP Configuration in the web interface: 1. -
Page 190: Upnp
3-20. UPnP UPnP is an acronym for Universal Plug and Play. The goals of UPnP are to allow devices to connect seamlessly and to simplify the implementation of networks in the home (data sharing, communications, and entertainment) and in corporate environments for simplified installation of computer components Web Interface To configure the UPnP Configuration in the web interface:... -
Page 191: Loop Protection
3-21 Loop Protection The loop detection is used to detect the presence of traffic. When switch receives packet’s (looping detection frame) MAC address the same as oneself from port, show Loop Protection happens. The port will be locked when it received the looping detection frames. If you want to resume the locked port, please find out the looping path and take off the looping path, then select the resume the locked port and click on “Resume”... - Page 192 Parameter description: Enable Loop Protection: Controls whether loop protections is enabled (as a whole). Transmission Time: The interval between each loop protection PDU sent on each port. valid values are 1 to 10 seconds. Shutdown Time: ...
-
Page 193: 3-21.2 Status
The period (in seconds) for which a port will be kept disabled in the event of a loop is detected (and the port action shuts down the port). Valid values are 0 to 604800 seconds (7 days). A value of zero will keep a port disabled (until next device restart). Port No: ... - Page 194 Parameter description: Port: The switch port number of the logical port Action: The currently configured port action Transmit: The currently configured port transmit mode. Loops: The number of loops detected on this port. Status: The current loop protection status of the port. Loop: ...
-
Page 195: Chapter 4. Security
Security Chapter 4. This chapter describes all of the switch security configuration tasks to enhance the security of local network including IP Source Guard, ARP Inspection,DHCP Snooping, AAA, and etc.. 4-1 IP Source Guard The section describes to configure the IP Source Guard detail parameters of the switch. You could use the IP Source Guard configure to enable or disable with the Port of the switch. - Page 196 Parameter description: Mode of IP Source Guard Configuration : Enable the Global IP Source Guard or disable the Global IP Source Guard. All configured ACEs will be lost when the mode is enabled. Port Mode Configuration : Specify IP Source Guard is enabled on which ports. Only when both Global Mode and Port Mode on a given port are enabled, IP Source Guard is enabled on this given port.
-
Page 197: 4-1.2 Static Table
4-1.2 Static Table The section describes to configure the Static IP Source Guard Table parameters of the switch. You could use the Static IP Source Guard Table configure to manage the entries. Web Interface To configure a Static IP Source Guard Table Configuration in the web interface: 1. -
Page 198: 4-1.3 Dynamic Table
4-1.3 Dynamic Table The section describes to configure the Dynamic IP Source Guard Table parameters of the switch. You could use the Dynamic IP Source Guard Table configure to manage the entries. Web Interface To configure a Dynamic IP Source Guard Table Configuration in the web interface: 1. -
Page 199: Arp Inspection
4-2 ARP Inspection The section describes to configure the ARP Inspection parameters of the switch. You could use the ARP Inspection configure to manage the ARP table. 4-2.1 Configuration This section describes how to configure ARP Inspection setting including: Mode (Enabled and Disabled) Port (Enabled and Disabled) Web Interface To configure an ARP Inspection Configuration in the web interface:... -
Page 200: 4-2.2 Static Table
4-2.2 Static Table The section describes to configure the Static ARP Inspection Table parameters of the switch. You could use the Static ARP Inspection Table configure to manage the ARP entries. Web Interface To configure a Static ARP Inspection Table Configuration in the web interface: 1. -
Page 201: 4-2.3 Dynamic Table
4-2.3 Dynamic Table The section describes to configure the Dynamic ARP Inspection Table parameters of the switch. The Dynamic ARP Inspection Table contains up to 1024 entries, and is sorted first by port, then by VLAN ID, then by MAC address, and then by IP address. Web Interface To configure a Dynamic ARP Inspection Table Configuration in the web interface: 1. -
Page 202: Dhcp Snooping
4-3 DHCP Snooping The section describes to configure the DHCP Snooping parameters of the switch. The DHCP Snooping can prevent attackers from adding their own DHCP servers to the network. 4-3.1 Configuration This section describes how to configure DHCP Snooping setting including: Snooping Mode (Enabled and Disabled) Port Mode Configuration (Trusted, Untrusted) Web Interface... -
Page 203: 4-3.2 Statistics
4-3.2 Statistics The section describes to show the DHCP Snooping Statistics information of the switch. The statistics show only packet counters when DHCP snooping mode is enabled and relay mode is disabled. And it doesn't count the DHCP packets for DHCP client. Web Interface To configure a DHCP Snooping Statistics Configuration in the web interface: 1. - Page 204 The number of lease unknown (option 53 with value 12) packets received and transmitted. Rx and Tx Lease Active : The number of lease active (option 53 with value 13) packets received and transmitted. Auto-refresh : To evoke the auto-refresh icon then the device will refresh the information automatically. Upper right icon (Refresh, Clear ): ...
-
Page 205: Dhcp Relay
4-4 DHCP Relay The section describes how to forward DHCP requests to another specific DHCP servers via DHCP relay. The DHCP servers may be on another network. 4-4.1 Configuration This section describes how to configure DHCP Relay setting including: Relay Mode (Enabled and Disabled) Relay Server IP setting Relay Information Mode (Enabled and Disabled) Relay Information Mode Policy (Replace, Keep and Drop) - Page 206 Disabled: Disable DHCP relay information mode operation. Relay Information Policy : Indicates the DHCP relay information option policy. When DHCP relay information mode operation is enabled, if agent receives a DHCP message that already contains relay agent information it will enforce the policy. And it only works under DHCP if relay information operation mode is enabled.
-
Page 207: 4-4.2 Statistics
4-4.2 Statistics The section describes to show the DHCP Relay Statistics information of the switch. The statistics show both of Server and Client packet counters when DHCP Relay mode is enabled. Web Interface To configure a DHCP Snooping Statistics Configuration in the web interface: 1. - Page 208 Replace Agent Option : The number of packets which were replaced with relay agent information option. Keep Agent Option : The number of packets whose relay agent information was retained. Drop Agent Option : The number of packets that were dropped which were received with relay agent information. Auto-refresh : ...
-
Page 209: Nas
4-5 NAS The section describes to configure the NAS parameters of the switch. The NAS server can be employed to connect users to a variety of resources including Internet access, conference calls, printing documents on shared printers, or by simply logging on to the Internet. 4-5.1 Configuration This section describes how to configure NAS setting of IEEE 802.1X, MAC-based authentication system, and port settings. - Page 210 Indicates if NAS is globally enabled or disabled on the switch. If globally disabled, all ports are allowed forwarding of frames. Reauthentication Enabled : If checked, successfully authenticated supplicants/clients are reauthenticated after the interval specified by the Reauthentication Period. Reauthentication for 802.1X-enabled ports can be used to detect if a new device is plugged into a switch port or if a supplicant is no longer attached.
-
Page 211: Port Configuration
server must be configured to transmit special RADIUS attributes to take advantage of this feature (see RADIUS-Assigned QoS Enabled below for a detailed description) The "RADIUS-Assigned QoS Enabled" checkbox provides a quick way to globally enable/disable RADIUS-server assigned QoS Class functionality. When checked, the individual ports' ditto setting determine whether RADIUS-assigned QoS Class is enabled on that port. - Page 212 Force Unauthorized : In this mode, the switch will send one EAPOL Failure frame when the port link comes up, and any client on the port will be disallowed network access. Port-based 802.1X : In the 802.1X-world, the user is called the supplicant, the switch is the authenticator, and the RADIUS server is the authentication server.
- Page 213 port (for instance through a hub) to piggy-back on the successfully authenticated client and get network access even though they really aren't authenticated. To overcome this security breach, use the Multi 802.1X variant. Multi 802.1X is really not an IEEE standard, but features many of the same characteristics as does port-based 802.1X.
- Page 214 RFC4675 forms the basis for identifying the QoS Class in an Access-Accept packet. Only the first occurrence of the attribute in the packet will be considered, and to be valid, it must follow this rule: • All 8 octets in the attribute's value must be identical and consist of ASCII characters in the range '0' - '3', which translates into the desired QoS Class in the range [0;...
-
Page 215: Port State
enabled, the port will now be placed in the Guest VLAN. If disabled, the switch will first check its history to see if an EAPOL frame has previously been received on the port (this history is cleared if the port link goes down or the port's Admin State is changed), and if not, the port will be placed in the Guest VLAN. -
Page 216: 4-5.2 Switch Status
4-5.2 Switch Status The section describes to show the each port NAS status information of the switch.The status includes Admin State Port State, Last Source, Last ID, QoS Class, and Port VLAN ID. Web Interface To configure a NAS Switch Status Configuration in the web interface: 1. - Page 217 about Guest VLANs here. Auto-refresh : To evoke the auto-refresh icon then the device will refresh the information automatically. Upper right icon (Refresh): You can click them for refresh the NAS Switch Status by manual.
-
Page 218: 4-5.3 Port Status
4-5.3 Port Status The section describes to provides detailed NAS statistics for a specific switch port running EAPOL-based IEEE 802.1X authentication. Web Interface To configure a NAS Port Status Configuration in the web interface: 1. Specify Port which want to check. 2. - Page 219 • Single 802.1X • Multi 802.1X Backend Server Counters : These backend (RADIUS) frame counters are available for the following administrative states: • Port-based 802.1X • Single 802.1X • Multi 802.1X • MAC-based Auth. Last Supplicant/Client Info : Information about the last supplicant/client that attempted to authenticate.
- Page 220 Shows the date and time of the last authentication of the client (successful as well as unsuccessful). Auto-refresh : To evoke the auto-refresh icon then the device will refresh the information automatically. Upper right icon (Refresh, Clear): You can click them for refresh the NAS Statistics by manual. Others you can click clear to clean up all entries.
-
Page 221: Aaa
4-6 AAA This section shows you to use an AAA (Authentication, Authorization, Accounting) server to provide access control to your network. The AAA server can be a TACACS+ or RADIUS server to create and manage objects that contain settings for using AAA servers. 4-6.1 Configuration This section describes how to configure AAA setting of TACACS+ or RADIUS server. - Page 222 Figure 4-5.3.3: The RADIUS Configuration Figure 4-5.3.4: The RADIUS Accounting Configuration Figure 4-5.3.4: The TACACS+ Authentication Configuration Parameter description: Timeout : The Timeout, which can be set to a number between 3 and 3600 seconds, is the maximum time to wait for a reply from a server. If the server does not reply within this timeframe, we will consider it to be dead and continue with the next enabled server (if any).
- Page 223 RADIUS Authentication Server Configuration The table has one row for each RADIUS Authentication Server and a number of columns, which are: The RADIUS Authentication Server number for which the configuration below applies. Enabled : Enable the RADIUS Authentication Server by checking this box. IP Address/Hostname : ...
- Page 224 Secret : The secret - up to 29 characters long - shared between the TACACS+ Authentication Server and the switch. Buttons: Save – Click to save changes. Reset- Click to undo any changes made locally and revert to previously saved values.
-
Page 225: 4-6.2 Radius Overview
4-6.2 Radius Overview This section shows you an overview of the RADIUS Authentication and Accounting servers status to ensure the function is workable. Web Interface To configure a RADIUS Overview Configuration in the web interface: 1. Checked “Auto-reflash”. Figure 4-6.2: The RADIUS Authentication Server Status Overview Parameter description: ... - Page 226 Ready: The server is enabled, IP communication is up and running, and the RADIUS module is ready to accept accounting attempts. Dead (X seconds left): Accounting attempts were made to this server, but it did not reply within the configured timeout. The server has temporarily been disabled, but will get re- enabled when the dead-time expires.
-
Page 227: 4-6.3 Radius Details
4-6.3 Radius Details This section shows you an detailed statistics of the RADIUS Authentication and Accounting servers. The statistics map closely to those specified in RFC4668 - RADIUS Authentication Client MIB. Web Interface To configure a RADIUS Details Configuration in the web interface: 1. -
Page 228: Port Security
4-7 Port Security This section shows you to to configure the Port Security settings of the Switch. You can use the Port Security feature to restrict input to an interface by limiting and identifying MAC addresses. 4-7.1 Limit Control This section shows you to to configure the Port Security settings of the Switch. You can use the Port Security feature to restrict input to an interface by limiting and identifying MAC addresses. - Page 229 Parameter description: System Configuration Mode : Indicates if Limit Control is globally enabled or disabled on the switch. If globally disabled, other modules may still use the underlying functionality, but limit checks and corresponding actions are disabled. Aging Enabled : ...
- Page 230 1) Boot the switch, 2) Disable and re-enable Limit Control on the port or the switch, 3) Click the Reopen button. Trap & Shutdown: If Limit + 1 MAC addresses is seen on the port, both the "Trap" and the "Shutdown"...
-
Page 231: 4-7.2 Switch Status
4-7.2 Switch Status This section shows the Port Security status. Port Security is a module with no direct configuration. Configuration comes indirectly from other modules - the user modules. When a user module has enabled port security on a port, the port is set-up for software-based learning. In this mode, frames from unknown MAC addresses are passed on to the port security module, which in turn asks all user modules whether to allow this new MAC address to forward or block it. - Page 232 Each of the user modules has a column that shows whether that module has enabled Port Security or not. A '-' means that the corresponding user module is not enabled, whereas a letter indicates that the user module abbreviated by that letter (see Abbr) has enabled port security.
-
Page 233: 4-7.3 Port Status
4-7.3 Port Status This section shows the MAC addresses secured by the Port Security module. Port Security is a module with no direct configuration. Configuration comes indirectly from other modules - the user modules. When a user module has enabled port security on a port, the port is set-up for software-based learning. -
Page 234: Access Management
4-8 Access Management This section shows you to configure access management table of the Switch including HTTP/HTTPS, SNMP, and TELNET/SSH. You can manage the Switch over an Ethernet LAN, or over the Internet. 4-8.1 Configuration This section shows you how to configure access management table of the Switch. The maximum entry number is 16. - Page 235 Indicates the end IP address for the access management entry. HTTP/HTTPS : Indicates that the host can access the switch from HTTP/HTTPS interface if the host IP address matches the IP address range provided in the entry. SNMP : ...
-
Page 236: 4-8.2 Statistics
4-8.2 Statistics This section shows you a detailed statistics of the Access Management including HTTP, HTTPS, SSH. TELNET, ans SSH. Web Interface To configure an Assess Management Statistics in the web interface: 1. Checked “Auto-refresh”. Figure 4-8.2: The Access Management Statistics Parameter description: Interface : ... -
Page 237: Ssh
4-9 SSH This section shows you to use SSH (Secure SHell) to securely access the Switch. SSH is a secure communication protocol that combines authentication and data encryption to provide secure encrypted communication. Web Interface To configure a SSH Configuration in the web interface: 1. -
Page 238: Https
4-10 HTTPs This section shows you how to use HTTPS to securely access the Switch. HTTPS is a secure communication protocol that combines authentication and data encryption to provide secure encrypted communication via the browser. Web Interface To configure a HTTPS Configuration in the web interface: 1. -
Page 239: Auth Method
4-11 Auth Method This page shows how to configure a user with authenticated when he logs into the switch via one of the management client interfaces. Web Interface To configure a Authentication Method Configuration in the web interface: 1. Specify the Client (console, telent, ssh, web) which you want to monitor. 2. -
Page 240: Chapter 5. Maintenance
Maintenance Chapter 5. This chapter describes the entire switch Maintenance configuration tasks to enhance the performance of local network including Restart Device, Firmware upgrade, Save/Restore, Import/Export, and Diagnostics. 5-1 Restart Device This section describes how to restart switch for any maintenance needs. Any configuration files or scripts that you saved in the switch should still be available afterwards. -
Page 241: Firmware
5-2 Firmware This section describes how to upgrade Firmware. The Switch can be enhanced with more value-added functions by installing firmware upgrades. 5-2.1 Firmware Upgrade This page facilitates an update of the firmware controlling the Switch. Web Interface To configure a Firmware Upgrade Configuration in the web interface: 1. -
Page 242: 5-2.2 Firmware Selection
5-2.2 Firmware Selection Due to the switch supports Dual image for firmware redundancy purpose. You can select what firmware image for your device start firmware or operating firmware. This page provides information about the active and alternate (backup) firmware images in the device, and allows you to revert to the alternate image. - Page 243 NOTE: 1. In case the active firmware image is the alternate image, only the "Active Image" table is shown. In this case, the Activate Alternate Image button is also disabled. 2. If the alternate image is active (due to a corruption of the primary image or by manual intervention), uploading a new firmware image to the device will automatically use the primary image slot and activate this.
-
Page 244: Save / Restore
5-3 Save / Restore This section describes how to save and restore the Switch configuration including reset to Factory Defaults, Save Start, Save Users, Restore Users for any maintenance needs. 5-3.1 Factory Defaults This section describes how to reset the Switch configuration to Factory Defaults. Any configuration files or scripts will recover to factory default values. -
Page 245: 5-3.3 Save User
Save – Click the “Save” button to save current setting as Start Configuration. 5-3.3 Save User This section describes how to save users information. Any current configuration files will be saved as XML format. Web Interface To configure a Save User Configuration in the web interface: 1. -
Page 246: Export / Import
5-4 Export / Import This section describes how to export and import the Switch configuration. Any current configuration files will be exported as XML format. 5-4.1 Export Config This section describes to export the Swith Configuration for maintenance needs. Any current configuration files will be exported as XML format. -
Page 247: 5-4.2 Import Config
5-4.2 Import Config This section describes to export the Swith Configuration for maintenance needs. Any current configuration files will be exported as XML format. Web Interface To configure an Import Config Configuration in the web interface: 1. Chick Browser to select the config file in you device. 2. -
Page 248: Diagnostics
5-5 Diagnostics This section provides a set of basic system diagnosis. It let users know that whether the system is health or needs to be fixed. The basic system check includes ICMP Ping, ICMPv6, and VeriPHY Cable Diagnostics 5-5.1 Ping This section allows you to issue ICMP PING packets to troubleshoot IPv6 connectivity issues. -
Page 249: 5-5.2 Ping6
5-5.2 Ping6 This section allows you to issue ICMPv6 PING packets to troubleshoot IPv6 connectivity issues. Web Interface To configure an ICMPv6 PING Configuration in the web interface: 1.Specify ICMPv6 PING IP Address 2.Specify ICMPv6 PING Size. 3.Click Start. Figure 5-5.2: The ICMPv6 Ping Parameter description: IP Address : ... -
Page 250: 5-5.3 Veriphy
5-5.3 VeriPHY This section is used for running the VeriPHY Cable Diagnostics. Press to run the diagnostics. This will take approximately 5 seconds. If all ports are selected, this can take approximately 15 seconds. When completed, the page refreshes automatically, and you can view the cable diagnostics results in the cable status table. -
Page 251: Glossary Of Web-Based Management
A. Glossary of Web-based Management ACE is an acronym for Access Control Entry. It describes access permission associated with a particular ACE ID. There are three ACE frame types (Ethernet Type, ARP, and IPv4) and two ACE actions (permit and deny). The ACE also contains many detailed, different parameter options that are available for individual application. -
Page 252: Arp Inspection
ARP is an acronym for Address Resolution Protocol. It is a protocol that used to convert an IP address into a physical address, such as an Ethernet address. ARP allows a host to communicate with other hosts when only the Internet address of its neighbors is known. Before using IP, the host sends a broadcast ARP request containing the Internet address of the desired destination system. -
Page 253: Dhcp Snooping
computer can be added to a network without the hassle of manually assigning it a unique IP address. DHCP Relay DHCP Relay is used to forward and to transfer DHCP messages between the clients and the server when they are not on the same subnet domain. The DHCP option 82 enables a DHCP relay agent to insert specific information into a DHCP request packets when forwarding client DHCP packets to a DHCP server and remove the specific information from a DHCP reply packets when forwarding server DHCP packets to a... - Page 254 Ethernet Type Ethernet Type, or EtherType, is a field in the Ethernet MAC header, defined by the Ethernet networking standard. It is used to indicate which protocol is being transported in an Ethernet frame. FTP is an acronym for File Transfer Protocol. It is a transfer protocol that uses the Transmission Control Protocol (TCP) and provides file writing and reading.
-
Page 255: Igmp Querier
IEEE 802.1X IEEE 802.1X is an IEEE standard for port-based Network Access Control. It provides authentication to devices attached to a LAN port, establishing a point-to-point connection or preventing access from that port if authentication fails. With 802.1X, access to all switch ports can be centrally controlled from a server, which means that authorized users can use the same credentials for authentication from any point within the network. - Page 256 LACP LACP is an IEEE 802.3ad standard protocol. The Link Aggregation Control Protocol, allows bundling several physical ports together to form a single logical port. The IEEE 802.2 Logical Link Control (LLC) protocol provides a link mechanism for upper layer protocols.
- Page 257 cryptographic hash function with a 128-bit hash value. It was designed by Ron Rivest in 1991. MD5 is officially defined in RFC 1321 - The MD5 Message-Digest Algorithm. Mirroring For debugging network problems or monitoring network traffic, the switch system can be configured to mirror frames from multiple ports to a mirror port.
- Page 258 Optional TLVs. A LLDP frame contains multiple TLVs For some TLVs it is configurable if the switch shall include the TLV in the LLDP frame. These TLVs are known as optional TLVs. If an optional TLVs is disabled the corresponding information is not included in the LLDP frame.
- Page 259 An alternative protocol is Internet Message Access Protocol (IMAP). IMAP provides the user with more capabilities for retaining e-mail on the server and for organizing it in folders on the server. IMAP can be thought of as a remote file server. POP and IMAP deal with the receiving of e-mail and are not to be confused with the Simple Mail Transfer Protocol (SMTP).
- Page 260 people or computers to connect and use a network service. RDI is an acronym for Remote Defect Indication. It is a OAM functionallity that is used by a MEP to indicate defect detected to the remote peer MEP RSTP In 1998, the IEEE with document 802.1w introduced an evolution of STP: the Rapid Spanning Tree Protocol, which provides for faster spanning tree convergence after a topology change.
-
Page 261: Tag Priority
authentication or guarantee confidentiality (Wikipedia). SSM In SyncE this is an abbreviation for Synchronization Status Message and is containing a QL indication. Spanning Tree Protocol is an OSI layer-2 protocol which ensures a loop free topology for any bridged LAN. The original STP protocol is now obsolete by RSTP. SyncE SyncE Is an abbreviation for Synchronous Ethernet. - Page 262 UDP is an acronym for User Datagram Protocol. It is a communications protocol that uses the Internet Protocol (IP) to exchange the messages between computers. UDP is an alternative to the Transmission Control Protocol (TCP) that uses the Internet Protocol (IP). Unlike TCP, UDP does not provide the service of dividing a message into packet datagrams, and UDP doesn't provide reassembling and sequencing of the packets.













Need help?
Do you have a question about the GTL-2880 and is the answer not in the manual?
Questions and answers