Summary of Contents for Clavister Eagle E20
- Page 1 Clavister Eagle E20 Getting Started Guide Clavister AB Sjögatan 6J SE-89160 Örnsköldsvik SWEDEN Phone: +46-660-299200 www.clavister.com Published 2016-01-13 Copyright © 2016 Clavister AB...
- Page 2 Clavister. Disclaimer The information in this document is subject to change without notice. Clavister makes no representations or warranties with respect to the contents hereof and specifically disclaims any implied warranties of merchantability or fitness for a particular purpose. Clavister reserves the right to revise this publication and to make changes from time to time in the content hereof without any obligation to notify any person or parties of such revision or changes.
-
Page 3: Table Of Contents
1. E20 Product Overview ..................7 1.1. Unpacking the E20 .................. 7 1.2. Interfaces and Ports ................. 9 2. Registering with Clavister .................. 11 3. E20 Installation ....................16 3.1. General Installation Guidelines ..............16 3.2. Flat Surface Installation ................18 3.3. -
Page 4: Table Of Contents
1.2. Clavister E20 Connection Ports ................9 1.3. The E20 Ethernet Interface Ports ................ 9 3.1. The E20 Mini-USB Local Console Port ..............21 3.2. Rear view of the Clavister E20 ................23 3.3. E20 Power Inlet Socket ..................23... -
Page 5: Preface
The target audience for this guide is the administrator who has taken delivery of a packaged Clavister E20 appliance and is setting it up for the first time. The guide takes the user from unpacking and installation of the device through to power-up, including network connections and initial cOS Core configuration. - Page 6 Where a "See section" link is provided in the main text, this can be clicked on to take the reader directly to that reference. For example, see Appendix A, E20 Specifications. Web links Web links included in the document are clickable. For example, http://www.clavister.com. Trademarks Certain names in this publication are the trademarks of their respective owners.
-
Page 7: E20 Product Overview
• Interfaces and Ports, page 9 1.1. Unpacking the E20 Figure 1.1. An Unpacked Clavister E20 Appliance This section details the unpacking of the E20 appliance. Open the packaging box used for shipping and carefully unpack the contents. The delivered product packaging should contain the following: •... - Page 8 Downloadable E20 Resources All documentation and other resources for the E20 can be downloaded from the E20 product page which can be found by going to http://www.clavister.com/start and selecting the E20 link. End of Life Treatment The E20 appliance is marked with the European Waste Electrical and Electronic Equipment (WEEE) directive symbol which is shown below.
-
Page 9: Interfaces And Ports
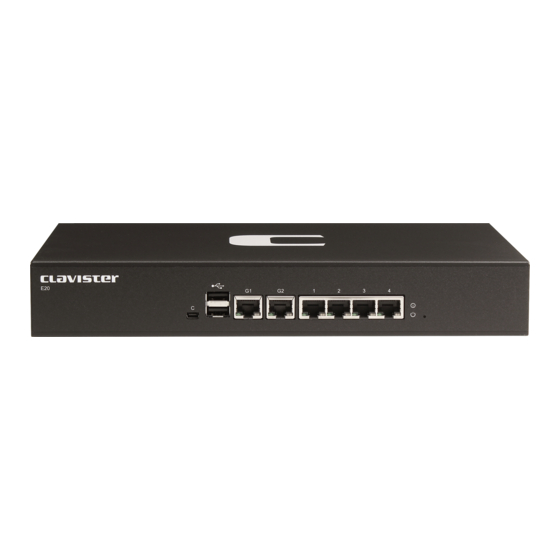
Chapter 1: E20 Product Overview 1.2. Interfaces and Ports This section is an overview of the E20 product's external design. Figure 1.2. Clavister E20 Connection Ports The E20 features the following connection ports on the front panel: • A mini-USB (type mini-B) port for console connection marked with the letter C. This port is used for direct access to the cOS Core Boot Menu and the cOS Core Command Line Interface (CLI). - Page 10 Chapter 1: E20 Product Overview...
-
Page 11: Registering With Clavister
The wizard is described in Section 4.2, “Web Interface and Wizard Setup”. Manual registration of the E20 on the Clavister website - This is described in the last half of this chapter. Manual registration may be necessary if the E20 does not have Internet access. - Page 12 Chapter 2: Registering with Clavister The customer login page is presented. It is assumed that a new customer is accessing the site for the first time so they should press the Register button. If already registered, log in and skip to step 8.
- Page 13 When the confirmation link in the email is clicked, the new customer is taken to a webpage to indicate that confirmation has been successful. They should now log in to the Clavister website with the credentials they have submitted during registration.
- Page 14 Core Setup Wizard which will appear as a browser popup window in the Web Interface when cOS Core starts for the first time. Log in to the Clavister website and select the Register License option. The registration page is displayed. Under the tab Hardware Serial Number and Service Tag, enter the Hardware Serial Number and Service Tag must be entered.
- Page 15 Once the E20 hardware unit is registered, a cOS Core license for the unit becomes available for download and installation from Clavister servers. This installation can be done automatically through the cOS Core Setup Wizard which is described in Section 4.2, “Web Interface and Wizard Setup”.
-
Page 16: E20 Installation
• Mini-USB Console Port Connection, page 21 • Connecting Power, page 23 3.1. General Installation Guidelines Follow these general guidelines when installing your Clavister E20 appliance: • Safety Take notice of the safety guidelines laid out in Chapter 7, Safety Precautions. These are specified in multiple languages. - Page 17 Chapter 3: E20 Installation • Surge Protection A third party surge protection device should be considered and is strongly recommended as a means to prevent electrical surges reaching the appliance. This is mentioned again in Section 3.5, “Connecting Power”. • Temperature Do not install the appliance in an environment where the ambient temperature during operation might fall outside the specified operating range.
-
Page 18: Flat Surface Installation
Chapter 3: E20 Installation 3.2. Flat Surface Installation The E20 can be mounted on any appropriate stable, flat, level surface that can safely support the weight of the appliance and its attached cables. Note: Attach the rubber feet provided with the E20 Adhesive rubber feet for the E20 unit are provided with the E20 in its packaging. -
Page 19: Rack Mounting
Chapter 3: E20 Installation 3.3. Rack Mounting A Rack Mount Kit is supplied with the E20 for mounting the product in a 19-inch rack. Included with the kit is the following: • 2 x side brackets. • 6 x bracket screws. 3 for securing one bracket to one side of the E20. The kit is attached to the sides of the E20 unit prior to mounting in the rack. - Page 20 Chapter 3: E20 Installation Repeat this for each side of the E20 so the brackets are mounted as shown below. The E20 is now ready to be rack mounted. No rear support is required.
-
Page 21: Mini-Usb Console Port Connection
For the Linux and MacOS micro-USB drivers or to download the Windows driver manually, go to the E20 product page which can be found at http://www.clavister.com/start. Direct the console emulator on the computer to connect to the newly installed device. After successful connection, commands can be issued to the cOS Core Command Line Interface (CLI). - Page 22 Chapter 3: E20 Installation Setup”. Connection Using SSH An alternative to using the local console port for CLI access is to connect via a physical Ethernet interface and using a Secure Shell (SSH) client on the management workstation to issue CLI commands.
-
Page 23: Connecting Power
Core will start. Important Please review the electrical safety information in Chapter 7, Safety Precautions. Figure 3.2. Rear view of the Clavister E20 Connecting AC Power To connect power, follow these steps: Plug the end of the power cord into the power inlet socket on the E20. - Page 24 Chapter 3: E20 Installation After a brief period of time, cOS Core will be fully initialized and the E20 is ready for configuration using a direct console connection or via the default management Ethernet interface. Initial cOS Core configuration is discussed in Chapter 4, cOS Core Configuration. Important: Protecting Against Power Surges It is recommended that the purchase and use of a separate surge protection unit from a third party is considered for the power connection to the E20 hardware.
- Page 25 Chapter 3: E20 Installation...
-
Page 26: Cos Core Configuration
It is assumed that the E20 unit is now unpacked, positioned correctly and power is applied. If not, the earlier chapters in this manual should be referred to before continuing. Clavister's cOS Core network security operating system is preloaded on the E20 and will automatically boot up after power is applied. After boot-up is complete, an external management computer workstation can be used to configure cOS Core. - Page 27 Chapter 4: cOS Core Configuration • Through a web browser. A standard web browser running on a standalone computer (also referred to as the management workstation) can be used to access the cOS Core Web Interface. This provides an intuitive graphical interface for cOS Core management. When this interface is accessed for the first time, a setup wizard runs automatically to guide a new user through key setup steps.
- Page 28 Chapter 4: cOS Core Configuration ISP and this is referred to in the setup wizard as the WAN interface. In this guide, it is assumed that the physical G2 interface of the E20 is used for Internet connection, although any other unused interface could be used instead.
-
Page 29: Web Interface And Wizard Setup
Chapter 4: cOS Core Configuration 4.2. Web Interface and Wizard Setup This chapter describes the setup when accessing cOS Core for the first time through a web browser. The user interface accessed in this way is called the Web Interface. It assumes that a physical network connection has been set up from a management computer to the default management Ethernet interface as described in Section 4.1, “Management Workstation Connection”. - Page 30 Chapter 4: cOS Core Configuration To continue, tell IE to accept the certificate by clicking the following link which appears near the bottom of the browser window. In Firefox, this procedure is called "Add a security exception". It is possible to configure cOS Core to use a CA signed certificate instead of self-signed certificate for the management login and doing this is described in the cOS Core Administration Guide.
- Page 31 The wizard assumes that Internet access will be configured. If this is not the case, for example if the Clavister Security Gateway is being used in Transparent Mode between two internal networks, then the configuration setup is best done with manual Web Interface steps or through the CLI instead of through the wizard and these are explained in the two sections that follow.
- Page 32 Chapter 4: cOS Core Configuration Wizard step 3: Select the WAN interface Next, you will be asked for the WAN interface that will be used to connect to an ISP for Internet access. Wizard step 4: Select the WAN interface settings This step selects how the WAN connection to the Internet will function.
- Page 33 Chapter 4: cOS Core Configuration These four different connection options are discussed next in the subsections 4A to 4D that follow. • 4A. Static - manual configuration Information supplied by the ISP should be entered in the next wizard screen. All fields need to be entered except for the Secondary DNS server field.
- Page 34 DNS servers are set automatically after connection with PPTP. Wizard step 5: DHCP server settings If the Clavister Security Gateway is to function as a DHCP server, it can be enabled here in the wizard on a particular interface or configured later.
- Page 35 Chapter 4: cOS Core Configuration Wizard step 6: Helper server settings Optional NTP and Syslog servers can be enabled here in the wizard or configured later. Network Time Protocol servers keep the system date and time accurate. Syslog servers can be used to receive and store log messages sent by cOS Core.
- Page 36 Once the wizard has been successfully finished and activated, it cannot be run again. The exception to this is if the Clavister Security Gateway has its factory defaults restored in which case the appliance will behave as though it were being started for the first time.
-
Page 37: Manual Web Interface Setup
Core. Ethernet Interfaces The physical connection of external networks to the Clavister Security Gateway is through the various Ethernet interfaces which are provided by the hardware platform. On first-time startup, cOS Core scans for these interfaces and determines which are available and allocates their names. - Page 38 Chapter 4: cOS Core Configuration Important: The time server URL requires the "dns:" prefix When specifying a URL in cOS Core for the time server, it must have the prefix "dns:". Once the values are set correctly, we can press the OK button to save the values while we move on to more steps in cOS Core configuration.
- Page 39 Reconfiguration is a process that the cOS Core administrator may initiate often. Normally, reconfiguration takes a brief amount of time and causes only a slight delay in traffic throughput. Active user connections through the Clavister Security Gateway should rarely be lost. Tip: How frequently to commit configuration changes It is up to the administrator to decide how many changes to make before activating a new configuration.
- Page 40 IPv4 address 10.5.4.1. The ISP's gateway is the first router hop towards the public Internet from the Clavister Security Gateway. Go to Objects > Address Book in the Web Interface. The current contents of the address book will be listed and will contain a number of predefined objects automatically created by cOS Core after it scans the interfaces for the first time.
- Page 41 Chapter 4: cOS Core Configuration On initial startup, two IPv4 address objects are created automatically for each interface detected by cOS Core. One IPv4 address object is named by combining the physical interface name with the suffix "_ip" and this is used for the IPv4 address assigned to that interface. The other address object is named by combining the interface name with the suffix "_net"...
- Page 42 At this point, the connection to the Internet is configured but no traffic can flow to or from the Internet since all traffic needs a minimum of the following two cOS Core configuration objects to exist before it can flow through the Clavister Security Gateway: •...
- Page 43 Chapter 4: cOS Core Configuration The empty main IP rule set will now appear. Press the Add button at the top left and select IP Rule from the menu. The properties for the new IP rule will appear. In this example, we will call the rule lan_to_wan. The rule Action is set to NAT (this is explained further below) and the Service is set to http which is suitable for most web browsing (it allows both HTTP and HTTPS connections).
- Page 44 For the Internet connection to work, a route also needs to be defined so that cOS Core knows on which interface the web browsing traffic should leave the Clavister Security Gateway. This route will define the interface where the network all-nets (in other words, any network) will be found. If the default main routing table is opened by going to Network >...
- Page 45 DHCP client. Usually, a DHCP Host Name does not need to be specified but can sometimes be used by an ISP to uniquely identify this Clavister Security Gateway as a particular DHCP client to the ISP's DHCP server.
- Page 46 Chapter 4: cOS Core Configuration For PPPoE connection, we must create a PPPoE tunnel interface associated with the physical Ethernet interface. Assume that the physical interface is G2 and the PPPoE tunnel object created is called wan_pppoe. Go to Network > Interfaces and VPN > PPPoE and select Add > PPPoE Tunnel.
- Page 47 DHCP Server Setup If the Clavister Security Gateway is to act as a DHCP server then this can be set up in the following way: First, create an IP4 Address object which defines the address range to be handed out. Here, it is assumed that this has the name dhcp_range.
- Page 48 Chapter 4: cOS Core Configuration An example IP pool range might be 196.168.1.10 - 192.168.1.20 with a netmask of 255.255.0.0. In addition, it is important to specify the Default gateway for the server. This will be handed out to DHCP clients on the internal networks so that they know where to find the public Internet. The default gateway is always the IPv4 address of the interface on which the DHCP server is configured, in this case, G1_ip.
- Page 49 As a further example of setting up IP rules, it can be very useful to allow ICMP Ping requests to flow through the Clavister Security Gateway. As discussed earlier, the cOS Core will drop any traffic unless an IP rule explicitly allows it. Let us suppose that we wish to allow the pinging of external hosts with the ICMP protocol by computers on the internal G1_net network.
- Page 50 The IP rule again has the NAT action and this is necessary if the protected local hosts have private IPv4 addresses. The ICMP requests will be sent out from the Clavister Security Gateway with the IP address of the interface connected to the ISP as the source interface. Responding hosts will send back ICMP responses to this single IP and cOS Core will then forward the response to the correct private IPv4 address.
- Page 51 Chapter 4: cOS Core Configuration Logging can now be enabled on this rule with the desired severity. Click the Log Settings tab, and click the Enable logging box. All log messages generated by this rule will be given the selected severity and this severity will appear in the text of the log messages. It is up to the administrator to choose the severity, depending on how they would like to classify the messages.
- Page 52 Chapter 4: cOS Core Configuration A Valid License Must Be Installed Lastly, a valid license should be installed to remove the cOS Core 2 hour demo mode limitation. Without a license installed, cOS Core will have full functionality during the 2 hour period following startup, but after that, only management access will be possible.
-
Page 53: Cli Setup
Chapter 4: cOS Core Configuration 4.4. CLI Setup This chapter describes the setup steps using CLI commands instead of the setup wizard. The CLI is accessible using either one of two methods: • Using an SSH (Secure Shell) client, across a network connection to the IPv4 address 192.168.1.1 on the default management Ethernet interface. - Page 54 Ethernet Interfaces The connection of external networks to the Clavister Security Gateway is via the various Ethernet interfaces which are provided by the hardware platform. On first-time startup, cOS Core determines which interfaces are available and allocates their names. One interface is chosen as the initial default management interface and this can only be changed after initial startup.
- Page 55 Chapter 4: cOS Core Configuration Note: Private IPv4 addresses are used for example only Each installation's IP addresses will be different from the example IP addresses but they are used here only to illustrate how setup is done. Also, these addresses are private IPv4 addresses and in reality an ISP would use public IPv4 addresses instead.
- Page 56 Chapter 4: cOS Core Configuration AutoDefaultGatewayRoute: ReceiveMulticastTraffic: Auto MemberOfRoutingTable: Comments: <empty> The typical output from this will be similar to the following: Setting the default gateway on the interface has the additional effect that cOS Core automatically creates a route in the default main routing table that has the network all-nets routed on the interface.
- Page 57 Chapter 4: cOS Core Configuration Assuming a second IP object called dns2_address has been defined, the second DNS server is specified with: Device:/> set DNS DNSServer2=dns2_address B. DHCP - automatic configuration Alternatively, all required IP addresses can be automatically retrieved from the ISP's DHCP server by enabling DHCP on the interface connected to the ISP.
- Page 58 30 second time period (this time period is a setting that can be changed). DHCP Server Setup If the Clavister Security Gateway is to act as a DHCP server then this can be set up in the following way:...
- Page 59 As a further example of setting up IP rules, it can be useful to allow ICMP Ping requests to flow through the Clavister Security Gateway. As discussed earlier, cOS Core will drop any traffic unless an IP rule explicitly allows it. Let us suppose that we wish to allow the pinging of external hosts with the ICMP protocol by computers on the internal G1_net network.
- Page 60 The IP rule again has the NAT action and this is necessary if the protected local hosts have private IPv4 addresses. The ICMP requests will be sent out from the Clavister Security Gateway with the IP address of the interface connected to the ISP as the source interface. Responding hosts will send back ICMP responses to this single IP and cOS Core will then forward the response to the correct private IP address.
-
Page 61: License Installation Methods
Core for another two hours. To remove this 2 hour restriction, a valid license must be installed. Licenses are files which are made available for download from the Clavister servers but before they become available, the user must have registered themselves with Clavister and doing this is described in Chapter 2, Registering with Clavister. - Page 62 CLI is only possible for the first time a license is installed. After that, future license installations can only be performed using the following two methods: • Manually, by logging into and downloading from the Clavister website and then uploading manually to cOS Core. •...
-
Page 63: Setup Troubleshooting
If the Input counters in the hardware section of the output are not increasing then the error is likely to be in the cabling. However, it may simply be that the packets are not getting to the Clavister Security Gateway in the first place. This can be confirmed with a packet sniffer if it is available. - Page 64 Chapter 4: cOS Core Configuration This will display console messages that show all the ARP packets being received on the different interfaces and confirm that the correct cables are connected to the correct interfaces. To look at the ARP activity only a particular interface, follow the command with the interface name: Device:/>...
-
Page 65: Going Further With Cos Core
IP rules identify the targeted traffic using combinations of the source/destination interface/network combined with protocol type. By default, no IP rules are defined so all traffic is dropped. At least one IP rule needs to be defined before traffic can traverse the Clavister Security Gateway. - Page 66 Staying Informed Clavister maintains an RSS feed of announcements that can be subscribed to at https://forums.clavister.com/rss-feeds/announcements/. It is recommended to subscribe to this feed so that you receive notifications when new releases of cOS Core versions are available for download and installation.
- Page 67 Chapter 4: cOS Core Configuration...
-
Page 68: Resetting To Factory Defaults
Chapter 5: Resetting to Factory Defaults In some circumstances, it may be necessary to reset the E20 hardware to the state it was in when it left the factory and was delivered to a customer. This process is known as a reset to factory defaults or simply a factory reset. - Page 69 If a console was connected in step 1, the console output will indicate that the hardware has been reset to its factory defaults. Release the button and the Clavister Security Gateway can now be configured as though it was brand new and had not previously been configured.
-
Page 70: Warranty Service
Start Date (as defined below). The warranty will only apply to failure of the product if Clavister is informed of the failure not later than two (2) years from the Start Date or thirty (30) days after that the failure was or ought to have been noticed by the customer. - Page 71 Chapter 6: Warranty Service If the product has not yet been registered with Clavister through its website, some proof of purchase (such as a copy of the dated purchase invoice) must be provided with the shipped product. Important: An RMA Number must be obtained before shipping! Any package returned to Clavister without an RMA number will be rejected and shipped back at the customer's expense.
-
Page 72: Safety Precautions
Chapter 7: Safety Precautions Safety Precautions Clavister E20 devices are Safety Class I products and have protective ground terminals. There must be an uninterrupted safety earth ground from the main power source to the product’s input wiring terminals, power cord, or supplied power cord set. Whenever it is likely that the protection has been impaired, disconnect the power cord until the ground has been restored. - Page 73 Chapter 7: Safety Precautions Informations concernant la sécurité Cet appareil est un produit de classe I et possède une borne de mise à la terre. La source d’alimentation principale doit être munie d’une prise de terre de sécurité installée aux bornes du câblage d’entree, sur le cordon d’alimentation ou le cordon de raccordement fourni avec le produit.
- Page 74 Chapter 7: Safety Precautions • se la vostra LAN copre un’area servita da più di un sistema di distribuzione elettrica, accertatevi che i collegamenti a terra di sicurezza siano ben collegati fra loro; • i cavi LAN possono occasionalmente andare soggetti a pericolose tensioni transitorie (ad esempio, provocate da lampi o disturbi nella griglia d’alimentazione della società...
-
Page 75: A. E20 Specifications
Appendix A: E20 Specifications Below are the key hardware specifications for the Clavister E20 product. Dimensions and Weight Height x Width x Depth (mm) 44 x 280 x 180 Hardware Weight 1.7 kg Hardware Form Factor Desktop 19-inch Rack Mountable... - Page 76 Clavister AB Sjögatan 6J SE-89160 Örnsköldsvik SWEDEN Phone: +46-660-299200 www.clavister.com...



Need help?
Do you have a question about the Eagle E20 and is the answer not in the manual?
Questions and answers