ZyXEL Communications P-2802HWL-I3 Manuals
Manuals and User Guides for ZyXEL Communications P-2802HWL-I3. We have 5 ZyXEL Communications P-2802HWL-I3 manuals available for free PDF download: User Manual, Support Notes, Quick Start Manual, Specifications, Declaration Of Conformity
ZyXEL Communications P-2802HWL-I3 User Manual (418 pages)
VDSL VoIP IAD
Brand: ZyXEL Communications
|
Category: Network Hardware
|
Size: 12.7 MB
Table of Contents
-
Introduction33
-
-
Overview35
-
-
Table 3 Leds40
-
Leds40
-
-
-
-
-
-
Introduction53
-
-
-
-
Introduction65
-
Advanced71
-
-
-
Any IP Table76
-
-
-
WAN Setup83
-
LAN Setup89
-
LAN IP Alias99
-
Wireless LAN101
-
Ssid102
-
Encryption103
-
Wpa(2)-Psk107
-
OTIST Screen111
-
Notes on OTIST113
-
MAC Filter114
-
-
-
LAN Overview89
-
DHCP Setup90
-
Lan Tcp/Ip90
-
Multicast92
-
RIP Setup92
-
Any IP93
-
DHCP Setup96
-
-
NAT Definitions117
-
-
How NAT Works118
-
NAT Application118
-
What NAT Does118
-
Port Forwarding121
-
Address Mapping125
-
Voice129
-
Rtp132
-
Voice Coding132
-
Diffserv134
-
VLAN Tagging135
-
Phone141
-
SIP Qos Screen141
-
The Flash Key145
-
Sip Alg128
-
-
Chapter 10 Voice
129-
Sip129
-
SIP Identities129
-
SIP Servers130
-
Speed Dial148
-
-
Triangle Route158
-
-
Threshold Values172
-
Ipsec179
-
VPN Overview179
-
VPN Applications180
-
Encapsulation181
-
Ipsec Algorithms181
-
Key Management181
-
Ipsec Algorithms185
-
VPN Screens185
-
My IP Address186
-
Keep Alive189
-
Pre-Shared Key193
-
IKE Phases198
-
Negotiation Mode199
-
Manual Key Setup202
-
Certificates211
-
Trusted cas221
-
Static Route235
-
-
-
-
-
My Certificates212
-
IEEE 802.1Q Tag239
-
Qos Overview239
-
Diffserv240
-
IP Precedence240
-
Qos Monitor248
-
-
-
-
Qos Example246
-
DYNDNS Wildcard251
-
-
-
-
System Timeout256
-
Telnet263
-
Configuring FTP264
-
Snmp265
-
Supported Mibs266
-
Configuring SNMP267
-
SNMP Traps267
-
Configuring DNS268
-
Configuring ICMP269
-
Www258
-
Login Screen261
-
-
HTTPS Example259
-
-
-
NAT Traversal271
-
Configuring Upnp272
-
Upnp and Zyxel272
-
-
General Setup285
-
System285
-
Time Setting287
-
Logs289
-
Introduction303
-
TFTP File Upload313
-
Diagnostic315
-
Troubleshooting317
-
Log Descriptions294
-
Restart309
-
-
Chapter 22 Logs
289 -
Chapter 23 Tools
303 -
Chapter 26
325
Advertisement
ZyXEL Communications P-2802HWL-I3 Support Notes (187 pages)
Zyxel P-2802HWL-I1: User Guide
Brand: ZyXEL Communications
|
Category: Wireless Router
|
Size: 3.35 MB
Table of Contents
-
Index
9 -
-
-
Using Syslog48
-
Faq
119-
Zynos FAQ119
-
What Is Zynos119
-
Change It120
-
-
Product FAQ123
-
What Is Pppoe124
-
What Is DDNS130
-
Voip FAQ133
-
Why Use Voip133
-
What Is Codec134
-
NAT Built-In138
-
Ipsec FAQ142
-
What Is PPTP143
-
What Is L2TP143
-
What Is Ipsec143
-
Wireless FAQ152
-
What Is 802.11B154
-
What Is 802.11A154
-
What Is 802.11G154
-
What Is Wi-Fi155
-
What Is an ESSID157
-
What Is 802.1X159
-
ZyXEL Communications P-2802HWL-I3 Quick Start Manual (16 pages)
802.11g Wireless VDSL VoIP IAD
Brand: ZyXEL Communications
|
Category: Network Router
|
Size: 2.3 MB
Table of Contents
Advertisement
ZyXEL Communications P-2802HWL-I3 Specifications (2 pages)
p-2802hw-i series 802.11g Wireless VDSL2 VoIP IAD
Brand: ZyXEL Communications
|
Category: Network Router
|
Size: 0.42 MB
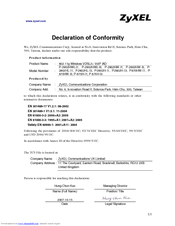
ZyXEL Communications P-2802HWL-I3 Declaration Of Conformity (2 pages)
802.11g Wireless VDSL2+ VoIP IAD
Brand: ZyXEL Communications
|
Category: VoIP
|
Size: 0.04 MB
Advertisement
Related Products
- ZyXEL Communications P-2802HW-I1
- ZyXEL Communications P-2802HW-I3
- ZyXEL Communications Prestige P-2802HWL-I1
- ZyXEL Communications P-2802H-I1
- ZyXEL Communications P-2802H-I3
- ZyXEL Communications P-2802HL-I1
- ZyXEL Communications P-2802HL-I3
- ZyXEL Communications P-2802HW-I
- ZyXEL Communications P-2802H-I Series
- ZyXEL Communications P-2802L-I Series